0%
Windows Internals
Learn and understand the fundamentals of how Windows operates at its core.
0%
Introduction to Windows API
Learn how to interact with the win32 API and understand its wide range of use cases
0%
Abusing Windows Internals
Leverage windows internals components to evade common detection solutions, using modern tool-agnostic approaches.
0%
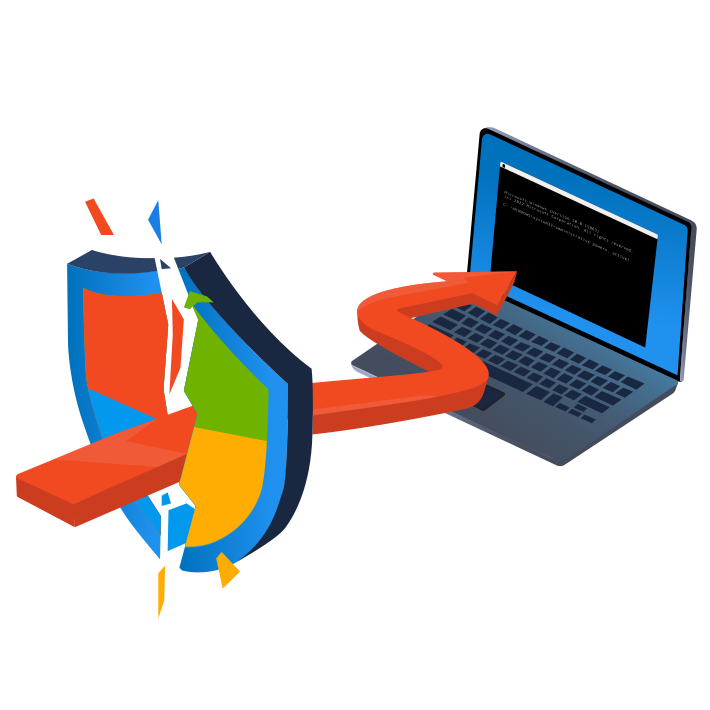
Introduction to Antivirus
Understand how antivirus software works and what detection techniques are used to bypass malicious file checks.
0%
AV Evasion: Shellcode
Learn shellcode encoding, packing, binders, and crypters.
0%
Obfuscation Principles
Leverage tool-agnostic software obfuscation practices to hide malicious functions and create unique code.
0%
Signature Evasion
Learn how to break signatures and evade common AV, using modern tool-agnostic approaches.
0%
Bypassing UAC
Learn common ways to bypass User Account Control (UAC) in Windows hosts.
0%
Runtime Detection Evasion
Learn how to bypass common runtime detection measures, such as AMSI, using modern tool-agnostic approaches.
0%
Evading Logging and Monitoring
Learn how to bypass common logging and system monitoring, such as ETW, using modern tool-agnostic approaches.
0%
Living Off the Land
Learn the essential concept of "Living Off the Land" in Red Team engagements.
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
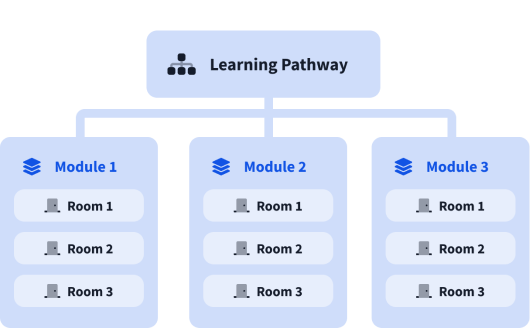
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).