0%
Attacktive Directory
challenge
99% of Corporate networks run off of AD. But can you exploit a vulnerable Domain Controller?
0%
Attacking Kerberos
walkthrough
Learn how to abuse the Kerberos Ticket Granting Service inside of a Windows Domain Controller
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
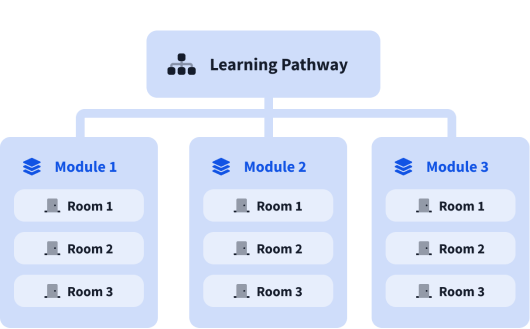
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).