To access material, start machines and answer questions login.
Press 'Start' to begin
This network is the continuation of the Breaching network. Please make sure to complete this network before continuing with this one. Also, note that we will discuss objects extensively. If you need a refresher, have a quick reskim of this room. Now that we have our very first set of valid Active Directory () credentials, we will explore the different methods that can be used to enumerate .
Enumeration
Once we have that first set of credentials and the means to authenticate with them on the network, a whole new world of possibilities opens up! We can start enumerating various details about the setup and structure with authenticated access, even super low-privileged access.
During a red team engagement, this will usually lead to us being able to perform some form of privilege escalation or lateral movement to gain additional access until we have sufficient privileges to execute and reach our goals. In most cases, enumeration and exploitation are heavily entwined. Once an attack path shown by the enumeration phase has been exploited, enumeration is again performed from this new privileged position, as shown in the diagram below.

Learning Objectives
In this network, we will cover several methods that can be used to enumerate . This is by no means a complete list as available methods are usually highly situational and dependent on the acquired breach. However, we will cover the following techniques for enumerating :
- The snap-ins of the Microsoft Management Console.
- The net commands of Command Prompt.
- The -RSAT cmdlets of .
- Bloodhound.
Connecting to the Network
AttackBox
If you are using the Web-based AttackBox, you will be connected to the network automatically if you start the AttackBox from the room's page. You can verify this by running the ping command against the IP of the THMDC.za.tryhackme.com host. We do still need to configure , however. Windows Networks use the Domain Name Service () to resolve hostnames to . Throughout this network, will be used for the tasks. You will have to configure on the host on which you are running the connection. In order to configure our , run the following command:
[thm@thm]$ sed -i '1s|^|nameserver $THMDCIP\n|' /etc/resolv-dnsmasq
nslookup thmdc.za.tryhackme.com
This should resolve to the IP of your DC.
Note:
may be reset on the AttackBox roughly every 3 hours. If this
occurs, you will have to redo the command above. If your
AttackBox terminates and you continue with the room at a later stage,
you will have to redo all the steps.
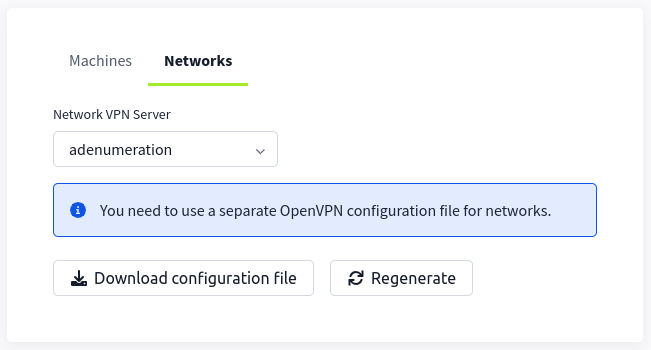
ifconfig or ip a, make note of the IP of the enumad network adapter. This is your IP and the associated interface that you should use when performing the attacks in the tasks.Other HostsIf you are going to use your own attack machine, an OpenVPN configuration file will have been generated for you once you join the room. Go to your access page. Select 'EnumeratingAD' from the VPN servers (under the network tab) and download your configuration file.
Use an OpenVPN client to connect. This example is shown on a Linux machine; similar guides to connect using Windows or macOS can be found at your access page.
[thm@thm]$ sudo openvpn adenumeration.ovpn
Fri Mar 11 15:06:20 2022 OpenVPN 2.4.9 x86_64-redhat-linux-gnu [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [PKCS11] [MH/PKTINFO] [AEAD] built on Apr 19 2020
Fri Mar 11 15:06:20 2022 library versions: OpenSSL 1.1.1g FIPS 21 Apr 2020, LZO 2.08
[....]
Fri Mar 11 15:06:22 2022 /sbin/ip link set dev tun0 up mtu 1500
Fri Mar 11 15:06:22 2022 /sbin/ip addr add dev tun0 10.50.2.3/24 broadcast 10.50.2.255
Fri Mar 11 15:06:22 2022 /sbin/ip route add 10.200.4.0/24 metric 1000 via 10.50.2.1
Fri Mar 11 15:06:22 2022 WARNING: this configuration may cache passwords in memory -- use the auth-nocache option to prevent this
Fri Mar 11 15:06:22 2022 Initialization Sequence Completed
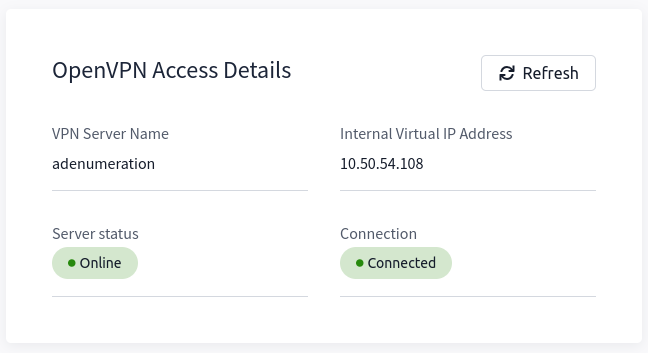
The message "Initialization Sequence Completed" tells you that you are now connected to the network. Return to your access page. You can verify you are connected by looking on your access page. Refresh the page, and you should see a green tick next to Connected. It will also show you your internal IP address.
Kali
If you are using a Kali VM, Network Manager is most likely used as DNS manager. You can use GUI Menu to configure DNS:
- Network Manager -> Advanced Network Configuration -> Your Connection -> IPv4 Settings
- Set your DNS IP here to the IP for THMDC in the network diagram above
- Add another DNS such as 1.1.1.1 or similar to ensure you still have internet access
- Run
sudo systemctl restart NetworkManagerand test your similar to the steps above.
Requesting Your Credentials
To simulate an AD breach, you will be provided with your first set of AD credentials. Once your networking setup has been completed, on your Attack Box, navigate to http://distributor.za.tryhackme.com/creds to request your credential pair. Click the "Get Credentials" button to receive your credential pair that can be used for initial access.
This credential pair will provide you RDP and SSH access to THMJMP1.za.tryhackme.com. THMJMP1 can be seen as a jump host into this environment, simulating a foothold that you have achieved. Jump hosts are often targeted by the red team since they provide access to a new network segment. You can use Remmina or any other similar Remote Desktop client to connect to this host for RDP. Remember to specify the domain of za.tryhackme.com when connecting. Task 2 and 3 will require RDP access.
For SSH access, you can use the following SSH command:
ssh za.tryhackme.com\\<AD Username>@thmjmp1.za.tryhackme.com
When prompted, provide your account's associated password. Although can be used for all tasks, is faster and can be used for Task 4, 5, and 6.
I have connected to the network and configured DNS.
I have requested my credential pair from the distributor and verified that I can RDP and SSH into THMJMP1.
Ready to learn Cyber Security?
The Enumerating Active Directory room is only available for premium users. Signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment.
Already have an account? Log in
