To access material, start machines and answer questions login.
Welcome to the team, kid. I have something for you to get your feet wet.
Our client has a newly hired employee who saw a suspicious-looking janitor exiting his office as he was about to return from lunch.
I want you to investigate if there was user activity while the user was away between 12:05 PM to 12:45 PM on the 19th of November 2022. If there are, figure out what files were accessed and exfiltrated externally.
You'll be accessing a live system, but use the disk image already exported to the C:\Users\THM-RFedora\Desktop\kape-results\C directory for your investigation. The link to the tools that you'll need is in C:\Users\THM-RFedora\Desktop\tools
Finally, I want to remind you that you signed an , so avoid viewing any files classified as top secret. I don't want us to get into trouble.
Connecting to the machine
Start the lab machine in split-screen view by clicking on the green "Start Lab Machine" button on the upper right section of this task. If the is not visible, use the blue "Show Split View" button at the top-right of the page. Alternatively, you can connect to the using the credentials below via "Remote Desktop".

| Username | -RFedora |
| Password | Passw0rd! |
| IP | MACHINE_IP |
Pre-requisites
This room is based on the Windows Forensics 1 and Windows Forensics 2 rooms. A cheat sheet is attached below, which you can also download by clicking on the blue Download Task Files button on the right.
To better understand how to perform forensics quickly and efficiently, consider checking out the room.
Good luck!
Initial investigations reveal that someone accessed the user's computer during the previously specified timeframe.
Whoever this someone is, it is evident they already know what to search for. Hmm. Curious.
What top-secret keyword was searched for using the search bar in Windows Explorer?
Not surprisingly, they quickly found what they are looking for in a matter of minutes.
Ha! They seem to have hit a snag! They needed something first before they could continue.
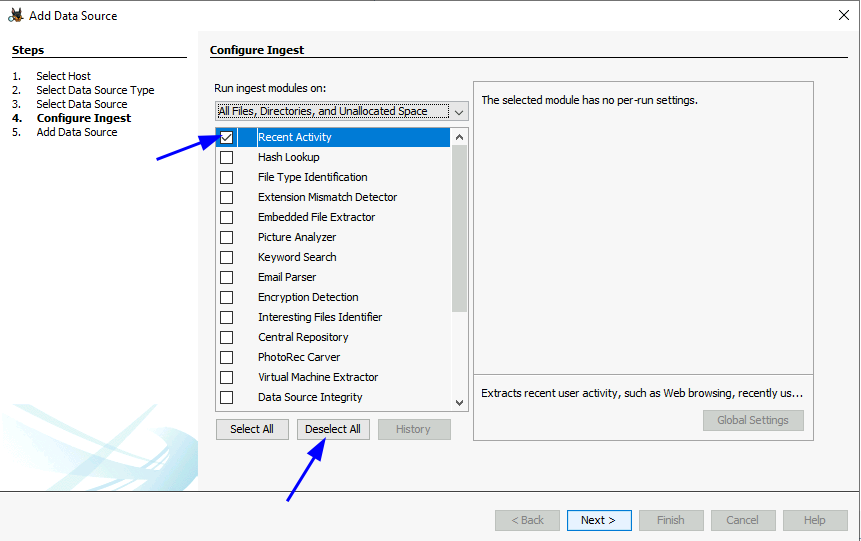
Note: When using the Autopsy Tool, you can speed up the load times by only selecting "Recent Activity" when configuring the Ingest settings.
When was the file from the previous question downloaded? (YYYY-MM-DD HH:MM:SS UTC)
Thanks to the previously downloaded file, a PNG file was opened. When was this file opened? (YYYY-MM-DD HH:MM:SS)
Uh oh. They've hit the jackpot and are now preparing to exfiltrate data outside the network.
There is no way to do it via USB. So what's their other option?
When was the text file from the previous question last modified? (MM/DD/YYYY HH:MM)
The contents of the file were exfiltrated to pastebin.com. What is the generated URL of the exfiltrated data?
What is the string that was copied to the pastebin URL?
At this point, we already have a good idea of what happened. The malicious threat actor was able to successfully find and exfiltrate data. While we could not determine who this person is, it is clear that they knew what they wanted and how to get it.
I wonder what's so important that they risked accessing the machine in-person... I guess we'll never know.
Anyways, you did good, kid. I guess it was too easy for you, huh?
Ready to learn Cyber Security?
TryHackMe provides free online cyber security training to secure jobs & upskill through a fun, interactive learning environment.
Already have an account? Log in
