To access material, start machines and answer questions login.
Ever caught wind of a new vulnerability on Twitter or found something weird when examining a box? Fear no more, AttackerKB is here to make sense of it all! Throughout this room, we'll be examining how we can leverage AttackerKB (opens in new tab) both as an attacker and defender to gain further insight into the ever-changing landscape of vulnerabilities.
A standalone version of the lab machine used in this room can be found in this room. Additionally, you can download the OVA of Source for offline usage from https://www.darkstar7471.com/resources.html (opens in new tab)
In this specific task, we'll be starting with the perspective of an attacker in a black-box assessment. Start by deploying and scanning the box in order to discover what has been installed.

Photo by Paweł Czerwiński (opens in new tab) on Unsplash
Scan the machine with Nmap. What non-standard service can be found running on the high-port?
Further enumerate this service, what version of it is running?
Visit the webpage generated by this service. You should encounter an error due to SSL being present. Change the URL to use HTTPS and ignore the exception. After this, view the certificate. What hostname can we find on the cert details? On Firefox, you can view this by clicking on the 'i' in the URL, then the '>' in Connection, 'More Information', and then 'View Certificate' on the Security tab.
Adjust your /etc/hosts file accordingly to include the newly discovered hostname and revisit the webpage in question. Note, that this will confirm that the service we previously discovered using Nmap is correct. Once you've done this, move onto task three.
Now that we've discovered a strange service running on our target, let's move onto further research to discover possible exploits and how valuable they might be with AttackerKB (opens in new tab).
First, let's navigate to AttackerKB (opens in new tab)! For our purposes, think of AttackerKB as similar to Exploit-DB but with a higher degree of information surrounding vulnerabilities and the exploits therein associated with them.
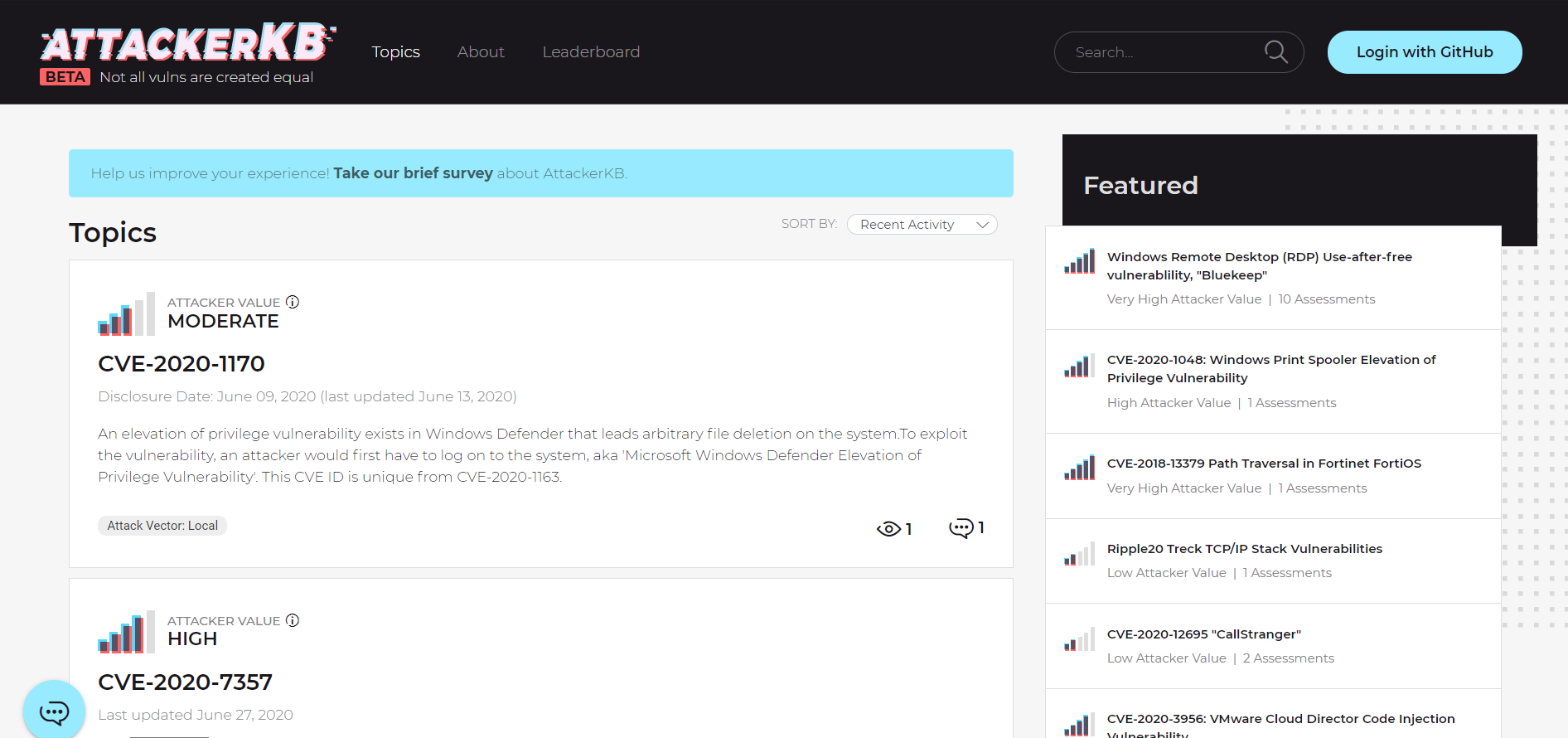
The AKB dashboard at the time of writing. Note, we won't have to log in for what we're doing. That being said, logging in (via GitHub OAuth) allows us to post and contribute to discussions surrounding vulnerabilities.
AKB allows us to search for various vulnerabilities via the search bar at the top right of the site. Search now for 'Webmin' and click on 'password_change.cgi'
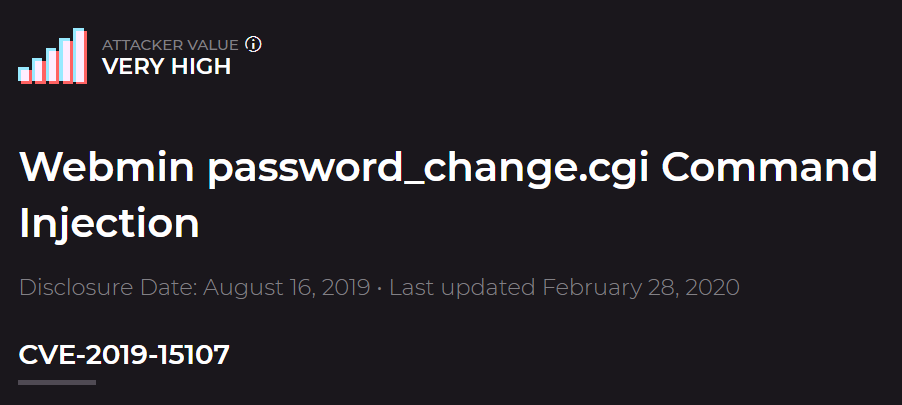
Take a look through the Assessments for this vulnerability. As an attacker, we can use the information posted here by other members to determine how value an exploit might be and any tweaks we might have to make to exploit code. Similarly, as a defender we can leverage these comments to gain additional situational information for vulnerabilities, allowing us to gauge how quickly we need to patch them. Which version of Webmin is immediately vulnerable to this exploit?
What type of attack was this? Note, we're looking for how this was added to the code for Webmin, not how this results in remote code execution (RCE).
Can you find a link to a post on the webmin's website explaining what happened? What day was Webmin informed of an 0day exploit?
Last but certainly not least, let's find the link to our exploit. We can see in the Assessments that a Metasploit module was added for this backdoor. What pull number was this added in?
Once you've located the exploit, let's move onto task four!
Now that we've gained some insight into the vulnerability and its associated exploit that we've discovered, let's move back into the scope of an attacker. In this task we'll be leveraging . If you have any difficulties here, I suggest checking out the RP: room
With Metasploit open, search for and select the exploit we previously investigated.
Now that we've selected our exploit, set the options provided appropriately. Beyond RHOSTS and LHOST, what is the third option we must set to 'True'?
Run the exploit. What is the user flag?
How about the root flag?
Once you've completed gaining the root flag, move onto the fifth and final task.
Want to get even more out of AttackerKB? Check out the AKB Explorer by Horshark! Written in python, AKB Explorer provides similar functionality to Searchsploit, expanded to encompass the features of AKB. Using this tool, you can search by name, , and username for posts! Check it out here: Link (opens in new tab)

Photo by Meiying Ng (opens in new tab) on Unsplash
Ready to learn Cyber Security?
TryHackMe provides free online cyber security training to secure jobs & upskill through a fun, interactive learning environment.
Already have an account? Log in

