To access material, start machines and answer questions login.
Virtual Private Cloud () (opens in new tab)is a software-defined-network construct in your account. It logically separates your network traffic from the network traffic of other Customers. Customers can define their CIDR ranges, connect their VPCs, or connect their VPCs to their on-premises networks.
VPCs are a regional construct. You need to create a in every region you want to deploy -based workloads.
By default, when a new account is created, default VPCs are deployed in all the standard regions. Each of these VPCs uses the same 172.31.0.0/16 CIDR Range. VPCs you create can use any CIDR range (you’re not limited to RFC1918 CIDR ranges).
You can see your VPCs on the Dashboard (opens in new tab). The dashboard is helpful because it allows you to view activity across all regions.
VPCs have a ID that begins with “-”. This ID is unique across all . used to be eight characters long, but in 2018 extended them to be 17 characters long. You can tell older VPCs by the short identifier.
Networking in a is different from networking in an on-premises environment. Because of the software-defined and multi-tenant nature of the public cloud, VPCs don't need things like to discover where the network devices reside. tables are visible for compatibility with the Operating System’s networking stack, but typical attack techniques like Spoofing will not work in a environment.
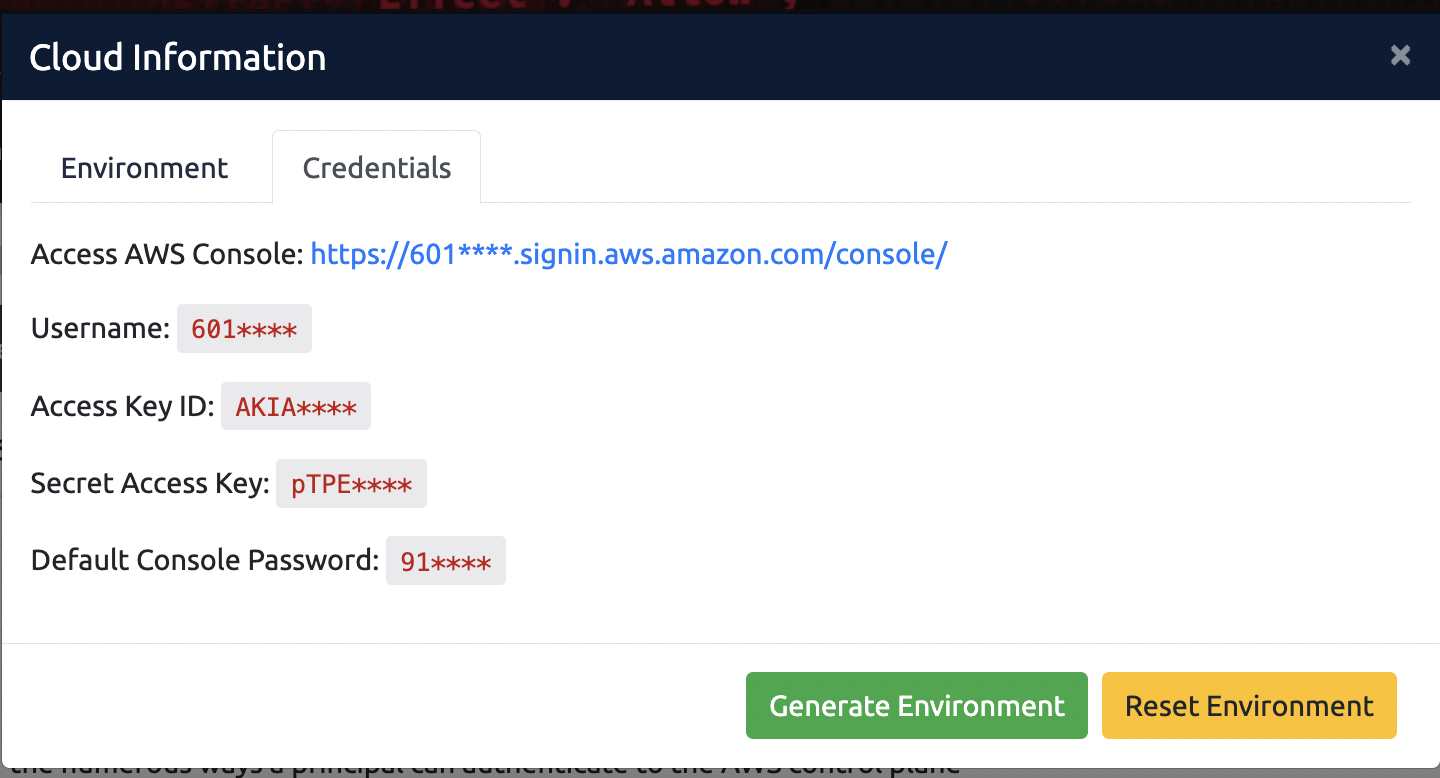
If you haven't already done so, click the orange Cloud Details button at the top-right of the page, generate the Cloud Environment, and use the Credentials provided to access your TryHackMe Cloud ( console).
Go to the Console (opens in new tab) and have a look around. Note: all resources are deployed in us-east-1 (N. Virginia).
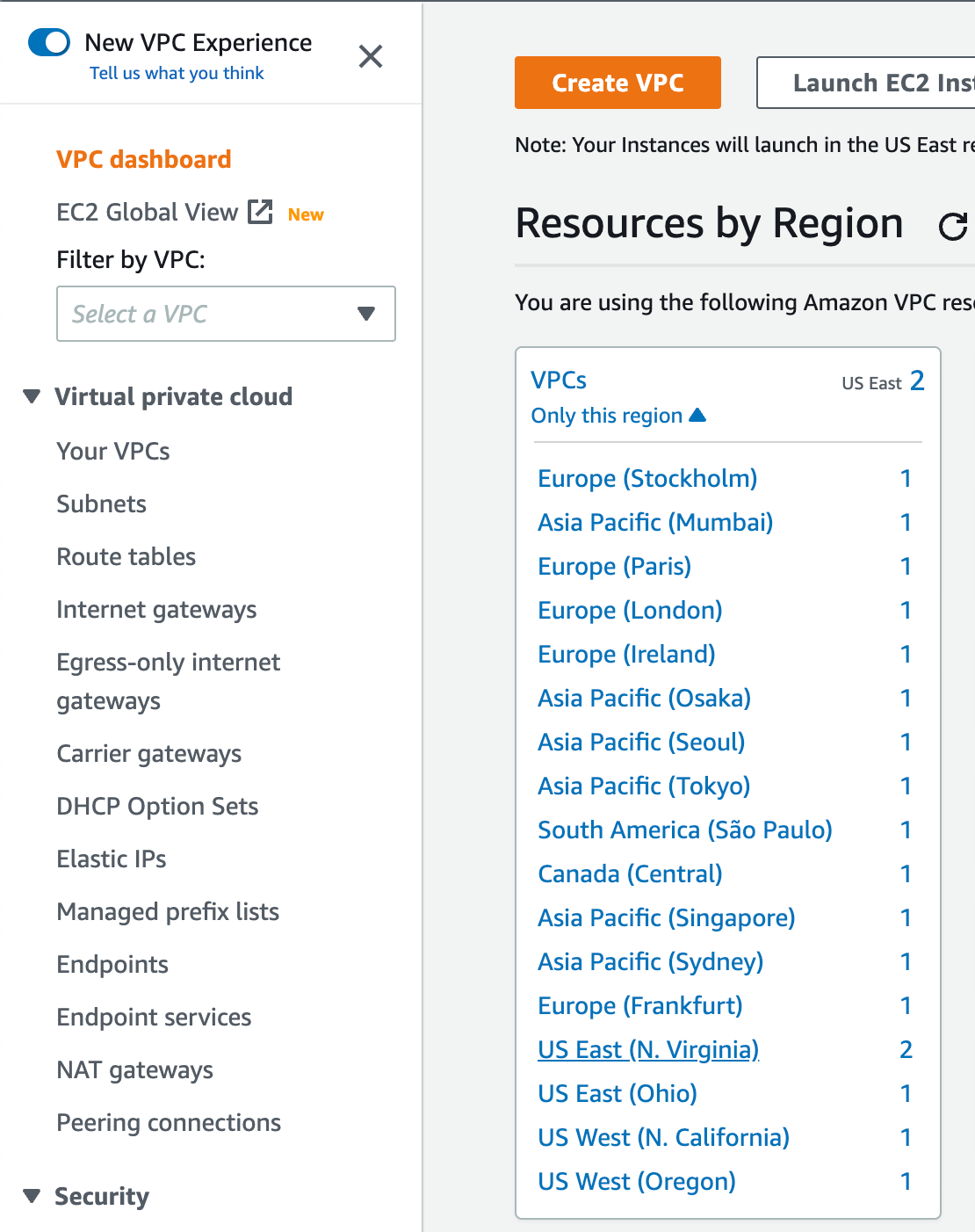
Global Listing of all VPCs. Note: for all the Try Hack Me labs, we will be using US East (N. Virginia), also known as us-east-1.
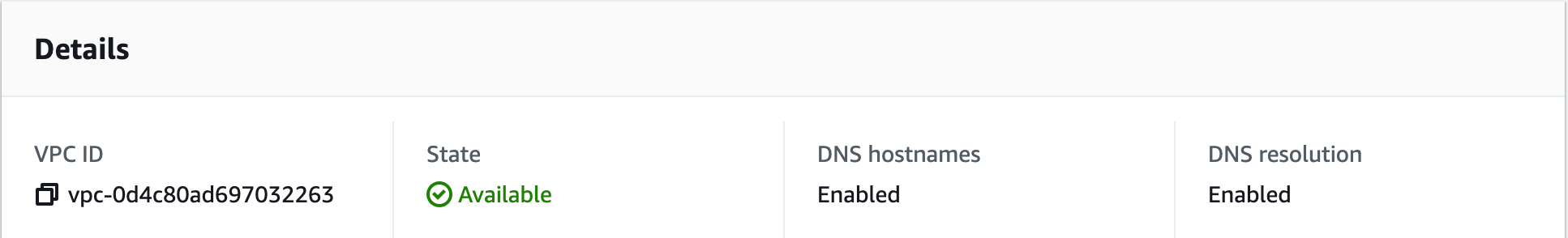
Sample ID in the Console
Select the Cloud details button at the top of the room:
Where needed generate the environment required for the room. The "Generate Environment" button will appear if the room contains an environment that needs to be generated.
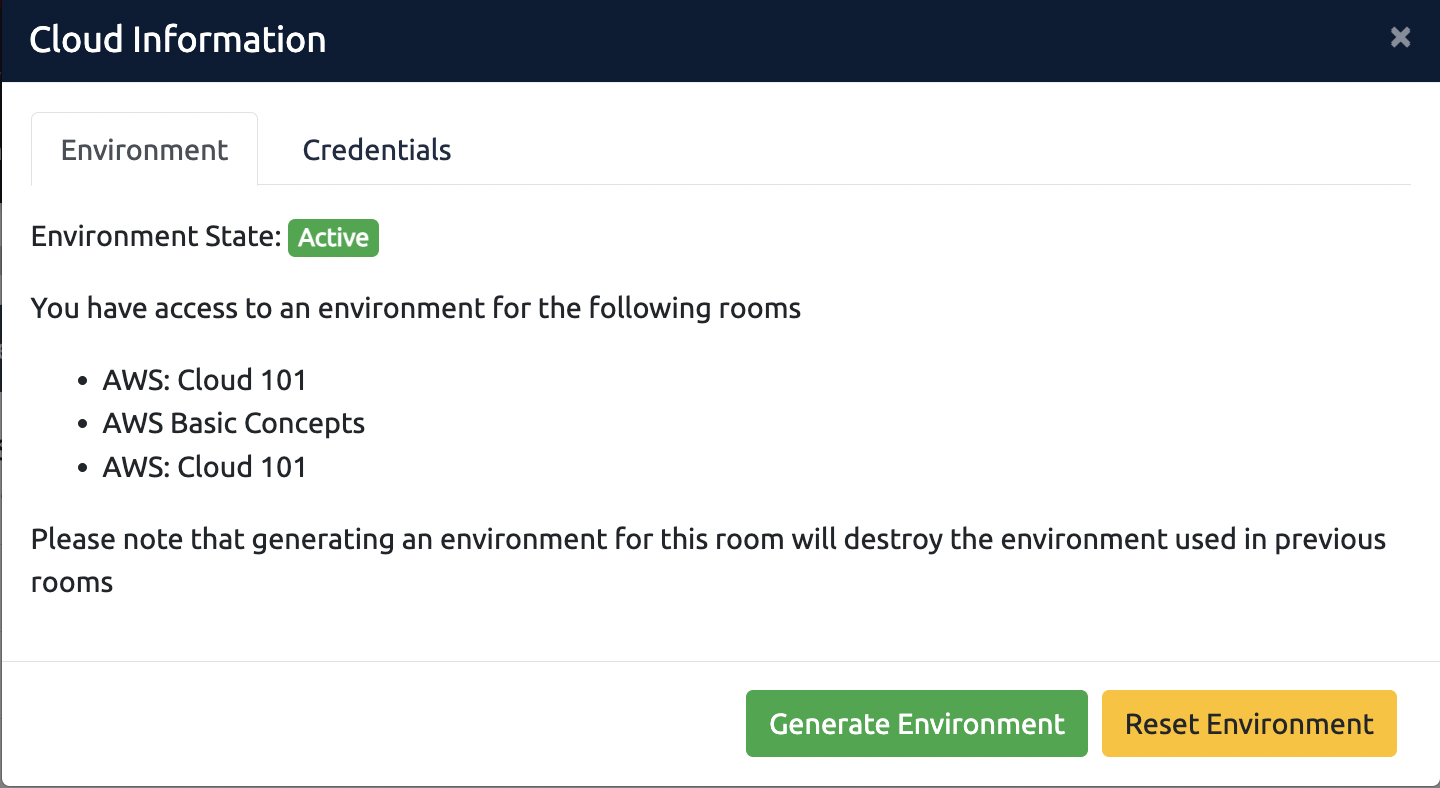
For any issues with the environment, select the "Reset Environment" button. Review this article for more information.
To view the credentials required for the environment, select the credentials tab. You can use these credentials to access the environment in various ways. More information can be found here:
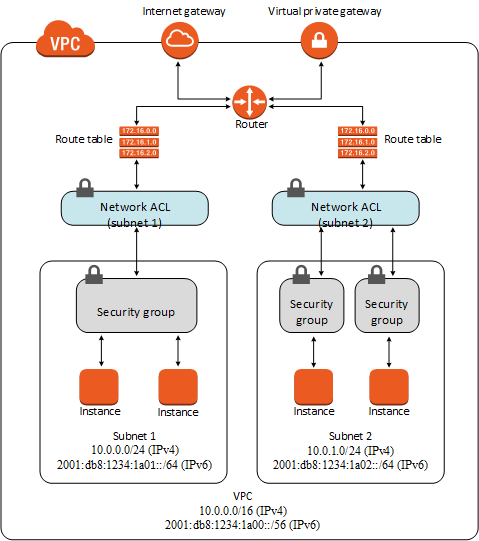
VPCs consist of Subnets, and each Subnet exists only in one Availability Zone (AZ). Subnets must use CIDR ranges that are subsets of the CIDR range, and Subnet CIDR ranges can’t overlap.
Every has a Router. Per 's Documentation:
| Your has an implicit router, and you use route tables to control where network traffic is directed. Each subnet in your must be associated with a route table, which controls the routing for the subnet (subnet route table). You can explicitly associate a subnet with a particular route table. Otherwise, the subnet is implicitly associated with the main route table. A subnet can only be associated with one route table at a time, but you can associate multiple subnets with the same subnet route table. |
VPCs have two special route destinations - Internet Gateway () and Virtual Private Gateway (VGW). The is the endpoint that acts as the border between the and the Internet. The VGW is the endpoint that acts as the border between the and on-premises networks.
You may hear the phrase "public subnet" or "private subnet" concerning Subnets. No attribute explicitly defines a subnet as a Public or Private Subnet. The only thing that makes a subnet “public” is how the route table sends traffic to the internet. If a subnet has a direct route to the , it is public, and any resource in that subnet with a public IP address is accessible from the internet. If there is no public IP address and no route to the , the subnet can be reasonably considered “private.” While a subnet could be configured to automatically assign a public IP address to Instances in the subnet, without a route to the , that Instance is not reachable from the internet.
As an attacker, you could modify the route table to make a subnet route to the and bypass some or all of the security controls. He who controls the controls the Network! -- Baron Harkonnen
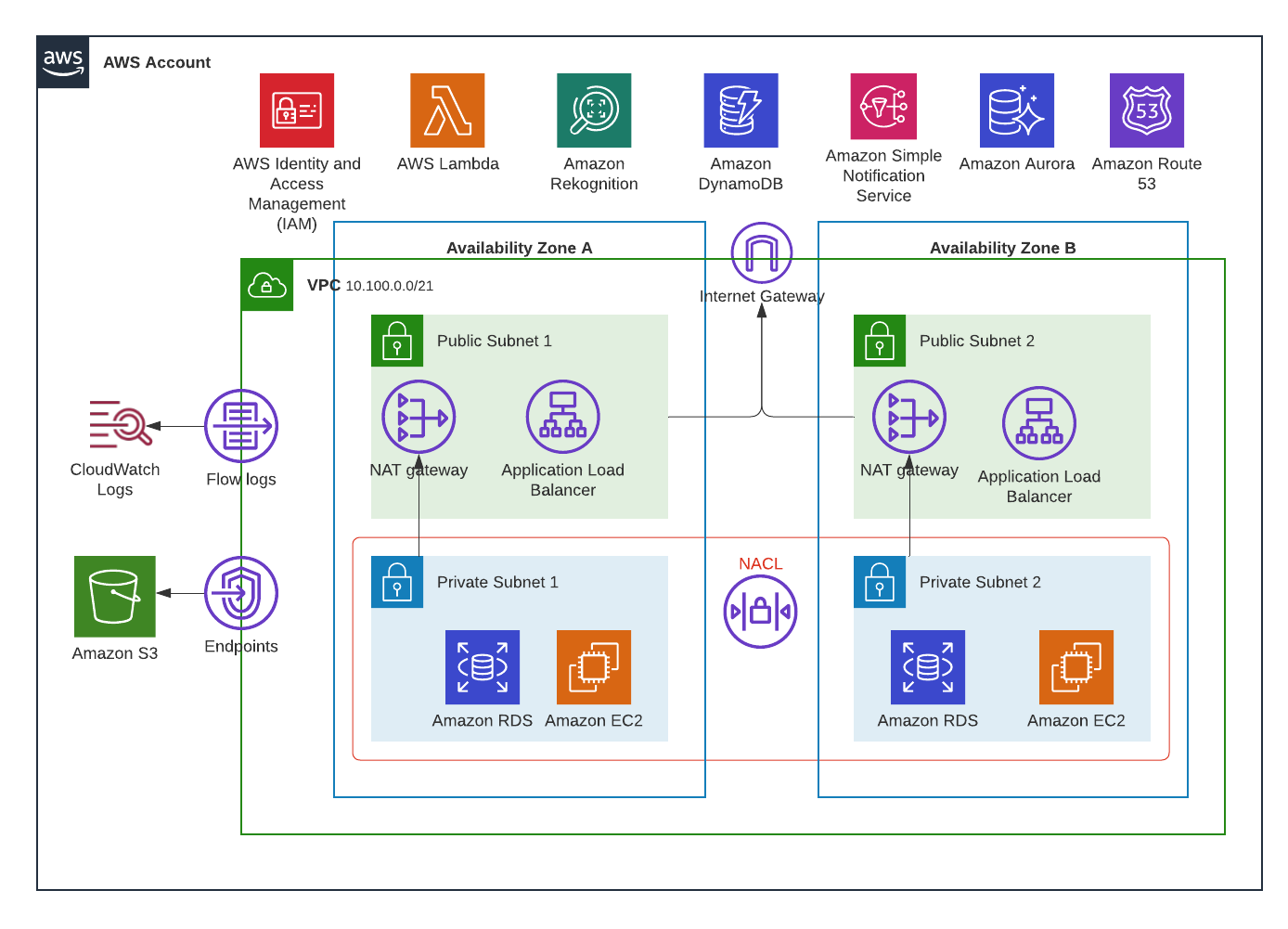
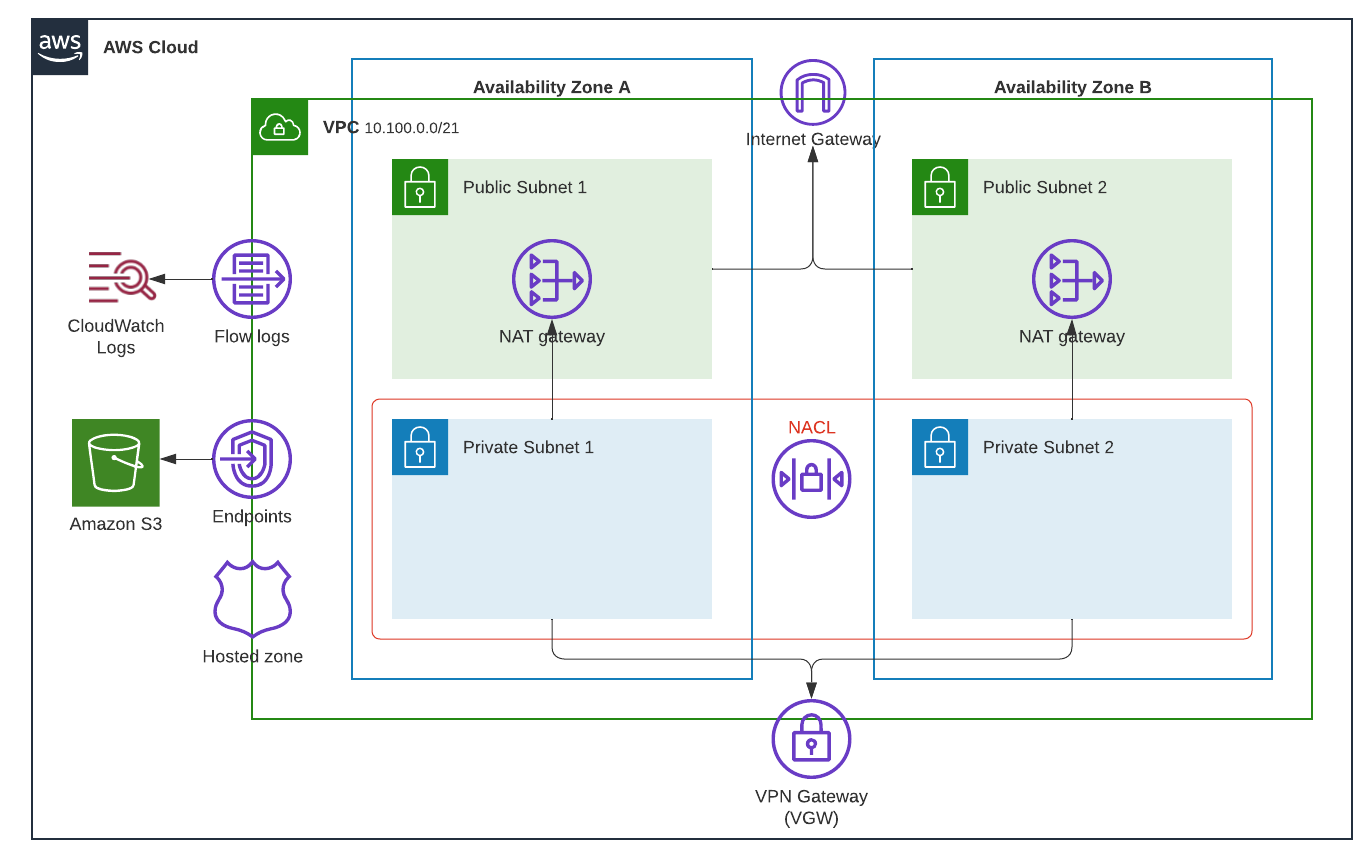 offers something called Managed NAT Gateways. These are Instances run by that provide NAT capabilities to allow private subnets to access the internet. You would typically configure your private subnet to route the 0.0.0.0/0 destination to the NAT Gateway, while you'd configure the route table of a public subnet to route the 0.0.0.0/0 destination to the directly.
offers something called Managed NAT Gateways. These are Instances run by that provide NAT capabilities to allow private subnets to access the internet. You would typically configure your private subnet to route the 0.0.0.0/0 destination to the NAT Gateway, while you'd configure the route table of a public subnet to route the 0.0.0.0/0 destination to the directly.
For the above diagram, your route tables might look like this:
Public Route Table 10.100.0.0/21 -> local 0.0.0.0/0 -> |
Private Route Table AZ-A 10.100.0.0/21 -> local 0.0.0.0/0 -> Nat Gateway A 10.0.0.0/8 -> VGW |
Private Route Table AZ-B 10.100.0.0/21 -> local 0.0.0.0/0 -> Nat Gateway B 10.0.0.0/8 -> VGW |
In the Public Subnets, all internet-facing traffic goes to the and the internet. For the two Private Subnets, traffic destined to the internet will go to the NAT Gateway in that AZ (for resiliency in case of an AZ failure). There is also a route to the on-prem corporate network (10.0.0.0/8) that points to the VGW. We'll discuss how on-prem networks talk to in a future room.
Network Access Control Lists, or NACLs, are one construct provides. NACLs apply to subnets. They are stateless in that both the initial (inbound) connection and the return (outbound) traffic must be authorized. NACLs support either Allow or Deny actions, and the actions are evaluated in a specific order. Unlike , an explicit Deny (opens in new tab) does not override an explicit Allow (opens in new tab). Instead, rules are processed in order until a match is made. By default, NACLs have a Deny All rule.
Here you can see how a is configured in the Console. In this specific case, the prohibits all Traffic, then allows all other traffic. The final Deny rule is the default from .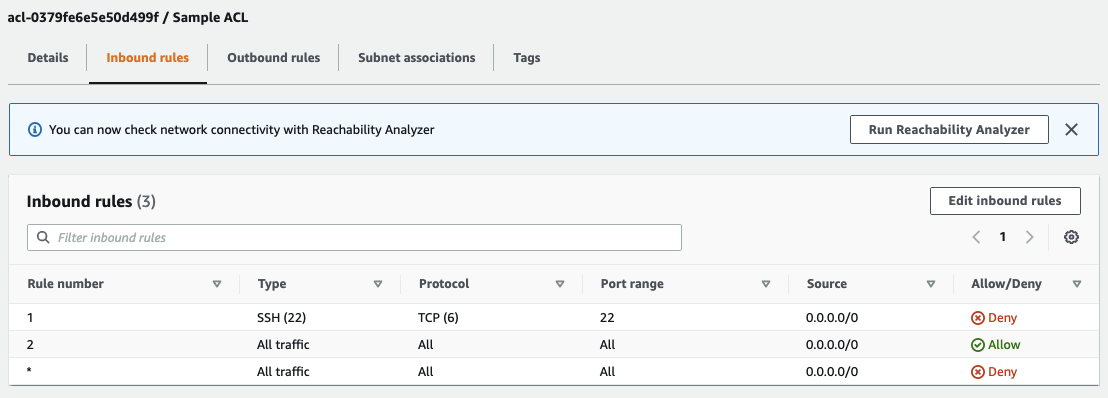
Because NACLs are applied to an entire subnet, they have a high-blast radius if misconfigured. For that reason, they’re used less frequently than the other form of network access control: security groups. Sometimes, a central network security team will configure NACLs for services they want to block with no exceptions.
Security Groups are attached to specific resources, such as an Instance or RDS Database. Security Groups only support allow. Security Groups are stateful and have different rule sets for Ingress (inbound) and Egress (outbound).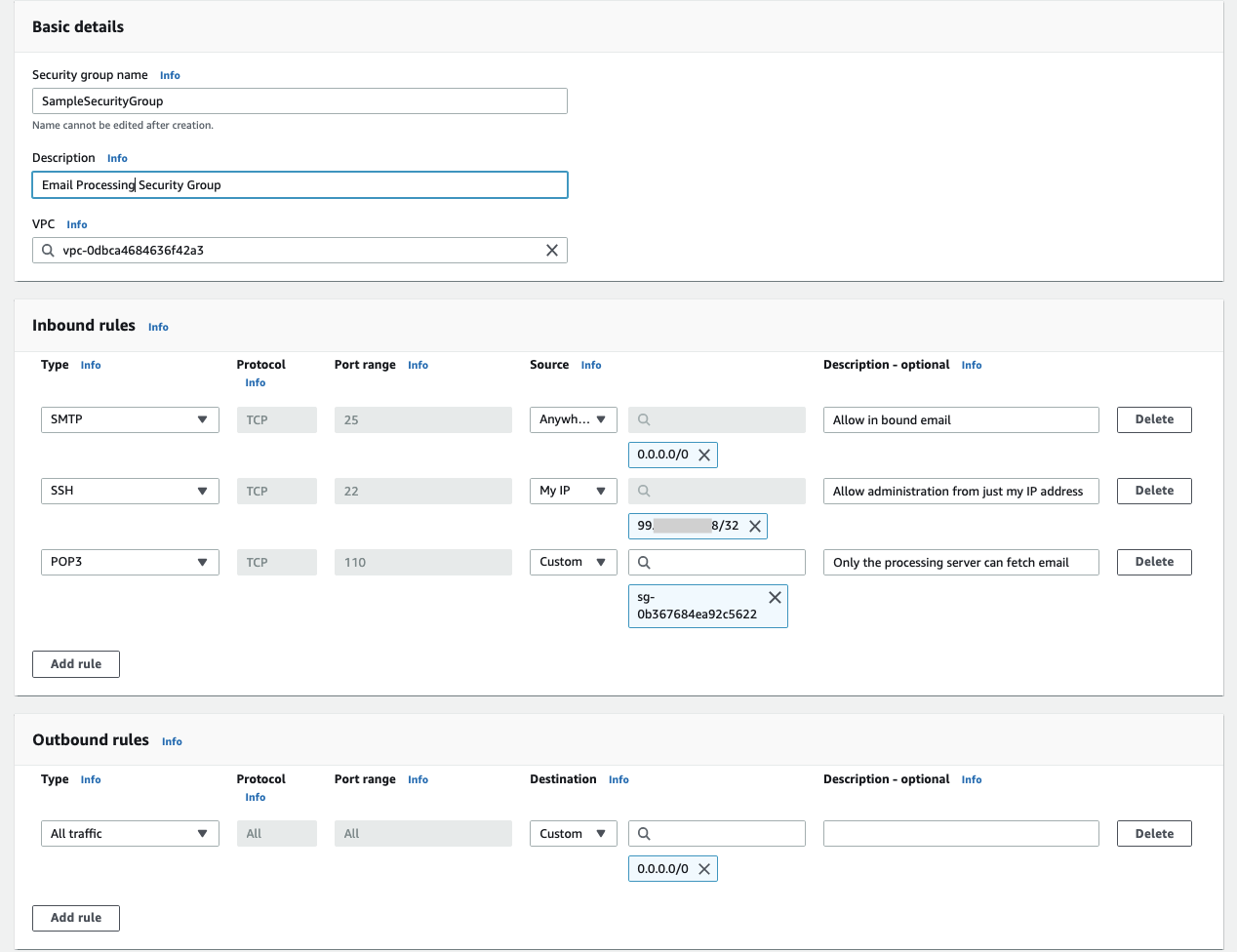
Security Groups are the primary way network-level access is managed for resources. Security Groups can reference either a CIDR range as a source or another Security Group ID. If a security group is referenced, any ENI with that Security Group attached is a valid source for the traffic.
The following table provided by summarizes the differences between Security Groups and NACLs (source (opens in new tab)):
Security group
|
Network
|
What port range is permitted to the private subnets from the on-prem network range?
An essential concept in defending your environment is knowing what resources reside inside a and which ones are outside the . Instances, RDS Databases, and big data things like RedShift are all examples of services that exist inside a . Whereas Buckets, the NoSQL Database DynamoDB, exist outside the .
Resources inside a can be protected via NACLs & Security groups, and you can prevent anyone from having direct access to them. Resources outside the are protected only by .
Every resource inside the has an Elastic Network Interface (opens in new tab) (ENI). ENIs are virtual network cards that are part of your . ENIs can be attached to an instance, detached, and moved to another instance (often, this is done to facilitate high-availability failover). ENIs represent a lease from the ’s server. ENIs can also have a public IPv4 address if configured as such. ENIs are tied to a specific subnet and can bridge an Instance across two subnets, but only in the same availability zone.
It is the ENI that security groups are attached to. You can get a holistic view of resources in a by listing all of the ENIs in an account. You can use the Console (opens in new tab) or the Command (via the CloudShell (opens in new tab)):
aws ec2 describe-network-interfacesList the ENIs in your account. What is the description of the ENI with the IP Address 10.100.2.79?
For resources inside a to talk to specific resources outside the , has created two related services: Endpoints and PrivateLink (opens in new tab). These services allow a network or security team to limit or completely disable internet egress in a .
Endpoints were first introduced with the Amazon service so that machines in a private subnet won’t need to leverage a NatGateway to access . NatGateways have a 1GB/s network limitation and can be somewhat expensive (opens in new tab). Before Endpoints, cloud architects were forced to put machines that require high-bandwidth operations on the internet to access . Endpoints work with and DynamoDB.
Endpoints require a route in the Route Table. The destination for the route is an abstract representation of the service, known as a Managed Prefix List (opens in new tab), rather than a specific CIDR Range.
uses Prefix Lists to map CIDR Ranges into your . These Prefix lists help manage its public IP addresses without requiring customers to change their Route tables or security groups. You can see the CIDR Ranges for the different services with the command:
aws ec2 describe-prefix-lists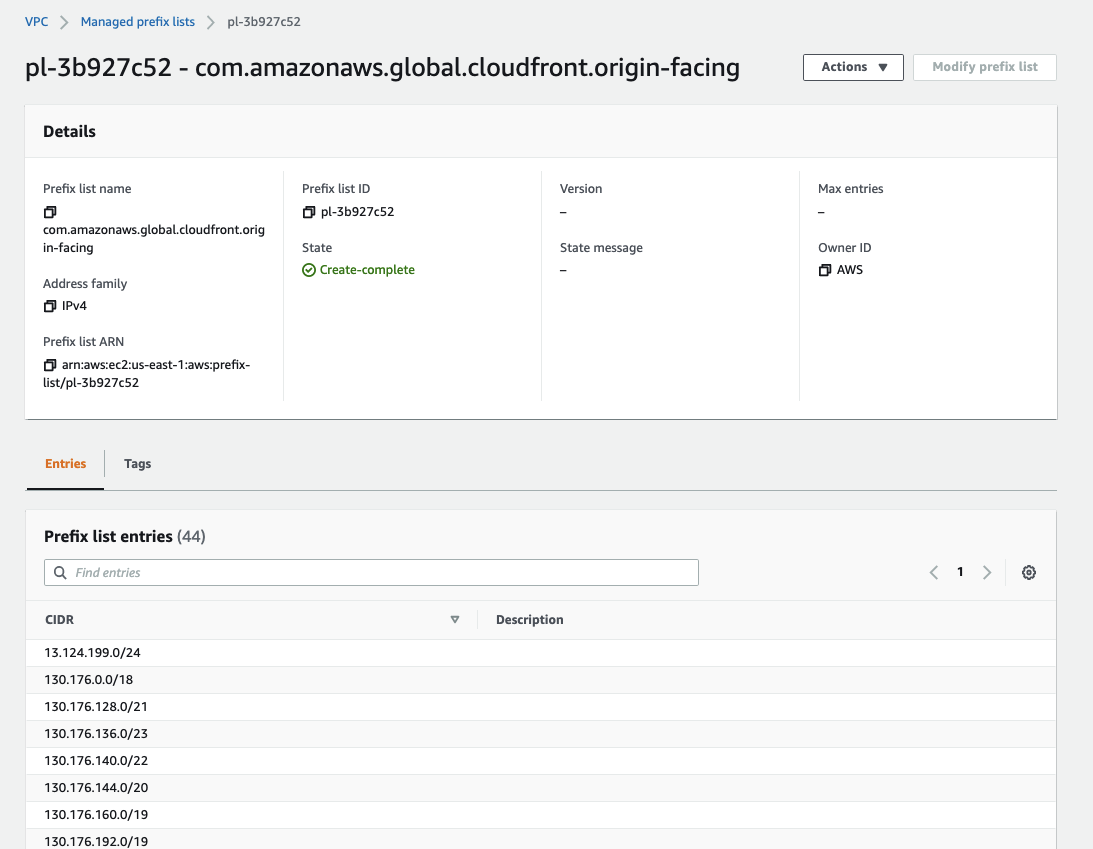
Endpoints can leverage to limit their use to specific Buckets or DynamoDB Tables. However, as an attacker, you could add a endpoint as a way to exfiltrate data from a into an bucket you control. Remember that trick when you get to your attack capstone project.
PrivateLink is an ENI in your tied to an Service or another Customer. It provides a way for or its partners to offer services to customers without requiring customers to allow traffic out to the internet. You can see here in the Console (opens in new tab) all the different PrivateLink services available:
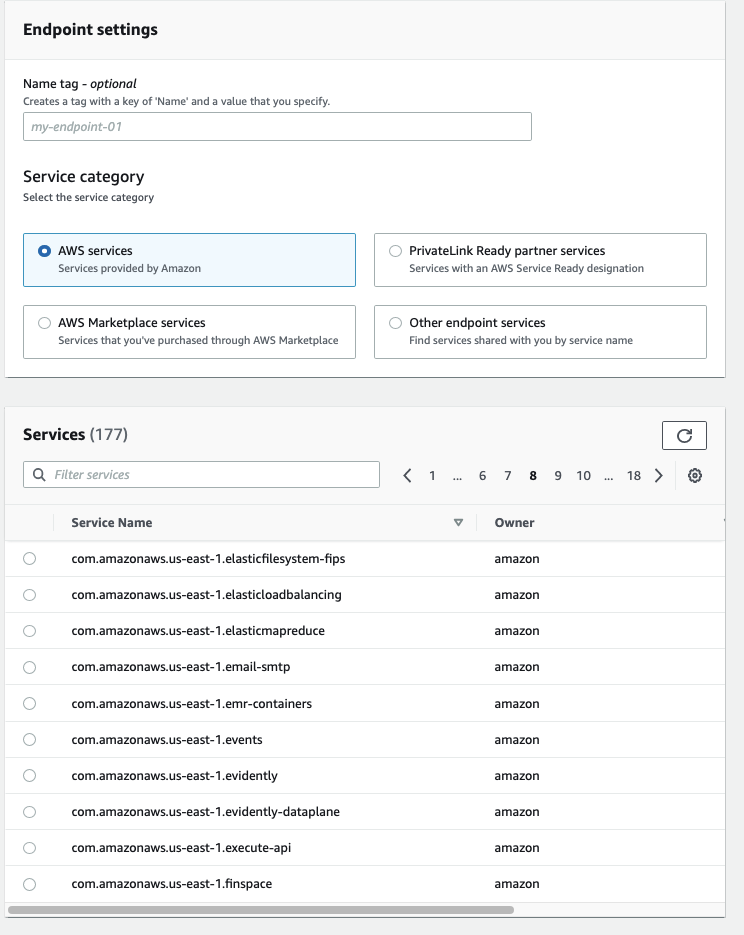
As you see above, there were 177 available services at the time of this screenshot. charges $0.01 per endpoint per hour. If you were to configure all 177 services for an entire month, you're looking at a $1,274.40 bill!
What is the service name for the VPC Endpoint?
has several services that can provide inside your . By default, instances in the will use the Amazon-provided server. That server is always at the “base of the IPv4 network range, plus two”. So if your CIDR is 192.168.15.0/24, then the default server will be 192.168.15.2. The Amazon server will resolve all public Entries.
You can also create a Private Route53 HostedZone and attach that to the . Route53 (opens in new tab) is Amazon’s hosted service. Route53 is a highly available, global service with advanced health checks and failover capabilities. We’ll discuss Route53 in more detail in a future module. For now, the critical concept is to know you can set up private entries (opens in new tab) that the Amazon provider will resolve for instances in your .
The ’s server can also be configured to answer requests from other networks (including on-premises networks) and to forward requests to on-prem servers. is another lateral movement path where compromise of the cloud can lead to the compromise of the corporate on-premises networks.
You can configure the Route 53 Resolver (opens in new tab) and Resolver Query Logging (opens in new tab) to Logs (opens in new tab) as a protection measure. The allows you to configure which domains the instances in your (and machines on-prem that leverage the Route53 Resolver) are allowed to query or not allowed to query. The serves as a mitigation mechanism for exfiltration attacks. Query logs will enable you to feed the activity of your Route53 Resolver to your Security Information and Event Management () for additional threat analysis.
Many of these advanced Route53 features have additional costs (opens in new tab), and you should realize when you’re incurring charges for security features.
Your is configured to send Logs to the log group “VPCResolverLogs.” You can view the entries from the Logs Console (opens in new tab). You can search the entire Log Group in the upper right with the orange “Search log group” box.
Within a , there are multiple ways of gathering security telemetry.
Flow Logs (opens in new tab) are like their cousin in that they log the packet headers but not the contents of the packet. The service can send the resulting logs to Logs or an Bucket. The latter is cheaper and provides a multi-account multi-regional approach by allowing enterprises to log to a central Bucket.
2 123456789012 eni-abcdef 52.46.145.233 10.100.0.118 443 52688 6 21 7010 1637966883 1637966911 ACCEPT OK| Each field has a specific meaning, as defined here (opens in new tab). The first field is the Flow Log version number (which will always be 2 if you’re using the defaults). Next is the account and the ENI identified. After that is the source and destination IP address, followed by the source and destination port. 6 represents the protocol number (). 21 is the number of packets, and 7010 is the number of bytes. The last four are the start and end times of the flow in Unix Epoch time, the action (ACCEPT or REJECT), and the log status (usually OK). |
In 2019, introduced Traffic Mirroring (opens in new tab). Traffic Mirroring acts as a network on a per ENI Basis and is useful for deep packet inspection. There are several limitations on where you can route the mirrored traffic. You need to have a layer-3 route from the source ENI to the traffic mirror target.
Logs (part of ), as discussed in the previous task, provide telemetry around what queries machines in your are making.
Amazon (opens in new tab) is a threat detection service. It leverages Threat Intelligence and Machine Learning to detect threats. For network threat detection, uses the and Logs.
provides several ways to connect to VPCs. As an attacker, it's helpful to know the multiple ways to move from the cloud to on-premise networks (Cloud-to-Ground) and between different VPCs (Cloud-to-Cloud). There is also a method for end-user access via an Managed Service called ClientVPN.
Cloud-to-Ground Connectivity
For enterprise customers, provides an interconnection service called DirectConnect (opens in new tab). For companies with racks at specific data centers (opens in new tab), will literally run a fiber-line from their cage to your router, giving you a dedicated link to the VGW in your . Bandwidth of the link can range from 1gbps to 100gbps. Customers can share these fiber lines across multiple VPCs and multiple accounts in the organization.
There is also the Site to Site (opens in new tab) for smaller organizations that don't need the level of bandwidth or latency Direct Connect provides. This service will initiate an IPSec (Internet Protocol Security) tunnel from to your on-premises router or .
With Site to Site , you first configure a Customer Gateway (opens in new tab) which defines the endpoint Site to Site will connect to. You then must create a connection that links the Customer Gateway with the Virtual Private Gateway (VGW).
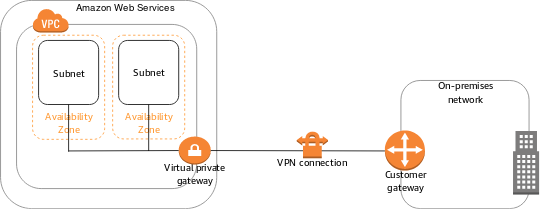
Both Direct Connect and Site to Site require a route in the routing table (opens in new tab). The on-premise networks need a target destination of the 's VGW to route the traffic.
From an attacker's perspective, this is a great way to pivot from the cloud to on-prem.
From a defender's perspective, you want to ensure that all Site to Site VPNs or DirectConnects terminate at a and set least-privilege rules.
From a compliance expert's standpoint, it's important to note that while Site to Site VPNs encrypt the traffic (since it's using IPSec), DirectConnect links are not encrypted as the traffic leaves your cage on its way to 's cage.
Cloud-to-Cloud Connectivity
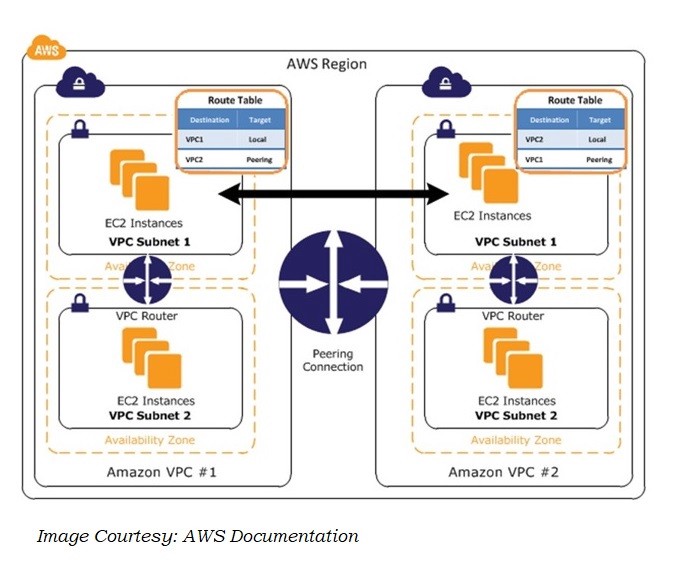
Many companies adopt a multi-account strategy (opens in new tab) to separate their development and production environments and limit the blast radius across development teams. When different teams need to communicate with each other's VPCs, provides two means:
Peering (opens in new tab) is a direct one-to-one method of allowing traffic to go from one to another inside 's network abstraction layer. Peered VPCs can reference each other's security groups. Peering works both across accounts and across regions. These features allow customers to replicate data to a disaster recovery setup that a development team should set up in different accounts and regions. Peering only works if the VPCs in question do not have overlapping CIDR Ranges.
Peering requires an entry in the route table for the peered 's CIDR range. The destination target for the route is the Peering endpoint.
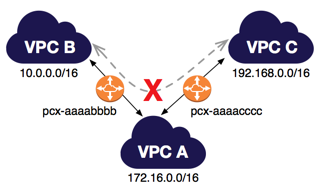
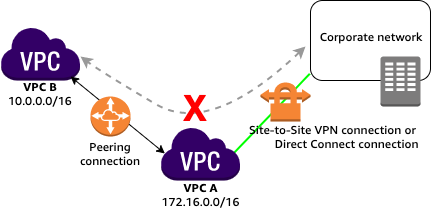
One essential concept related to Peering is that routing is not transitive with Peering. If -A has peered to -B, and -B has peered to -C, there is no network path for a machine in -A to talk directly to an IP Address in -C. The machine in -A would have to talk to a device in -B, which could then forward that to -C. The same transitive routing limitation applies to and DirectConnect connections.
Transit Gateway (opens in new tab) was intended to solve the management of connections by creating an inter- router. Rather than requiring a direct peering connection between each that needs to pass traffic, the Transit Gateway allows all of them to interconnect and supports DirectConnect and Site to Site .
Client
One final service attackers and defenders should be aware of is Client (opens in new tab). Client is best described as "Bypass the Corporate and Access Controls as-a-Service." It allows anyone with privileged access to an account to set up their own -managed OpenVPN service.
Customers can configure client VPNs to use three different methods of authentication (opens in new tab): shared certificates, 's Single Sign-On offering, or 's managed Microsoft Active Directory. In each case, the controls for Multi-Factor Authentication (), identity management, and audit logging are no longer under the control of central IT but are managed by the team running the account. This makes Client a potential security and compliance risk if not configured correctly.
What is the routing target prefix for the VPC Peering connection?
Ready to learn Cyber Security?
TryHackMe provides free online cyber security training to secure jobs & upskill through a fun, interactive learning environment.
Already have an account? Log in
