To access material, start machines and answer questions login.
This room will cover all of the basics of attacking the windows ticket-granting service; we'll cover the following:
- Initial enumeration using tools like Kerbrute and Rubeus
- Kerberoasting
- AS-REP Roasting with Rubeus and Impacket
- Golden/Silver Ticket Attacks
- Pass the Ticket
- Skeleton key attacks using mimikatz
This room will be related to very real-world applications and will most likely not help with any CTFs however it will give you great starting knowledge of how to escalate your privileges to a domain admin by attacking and allow you to take over and control a network.
It is recommended to have knowledge of general post-exploitation, active directory basics, and windows command line to be successful with this room.

What is ? -
is the default authentication service for Microsoft Windows domains. It is intended to be more "secure" than by using third party ticket authorization as well as stronger encryption. Even though has a lot more attack vectors to choose from still has a handful of underlying vulnerabilities just like that we can use to our advantage.
Common Terminology -
- Ticket Granting Ticket () - A ticket-granting ticket is an authentication ticket used to request service tickets from the TGS for specific resources from the domain.
- Key Distribution Center (KDC) - The Key Distribution Center is a service for issuing TGTs and service tickets that consist of the Authentication Service and the Ticket Granting Service.
- Authentication Service (AS) - The Authentication Service issues TGTs to be used by the TGS in the domain to request access to other machines and service tickets.
- Ticket Granting Service (TGS) - The Ticket Granting Service takes the and returns a ticket to a machine on the domain.
- Service Principal Name (SPN) - A Service Principal Name is an identifier given to a service instance to associate a service instance with a domain service account. Windows requires that services have a domain service account which is why a service needs an SPN set.
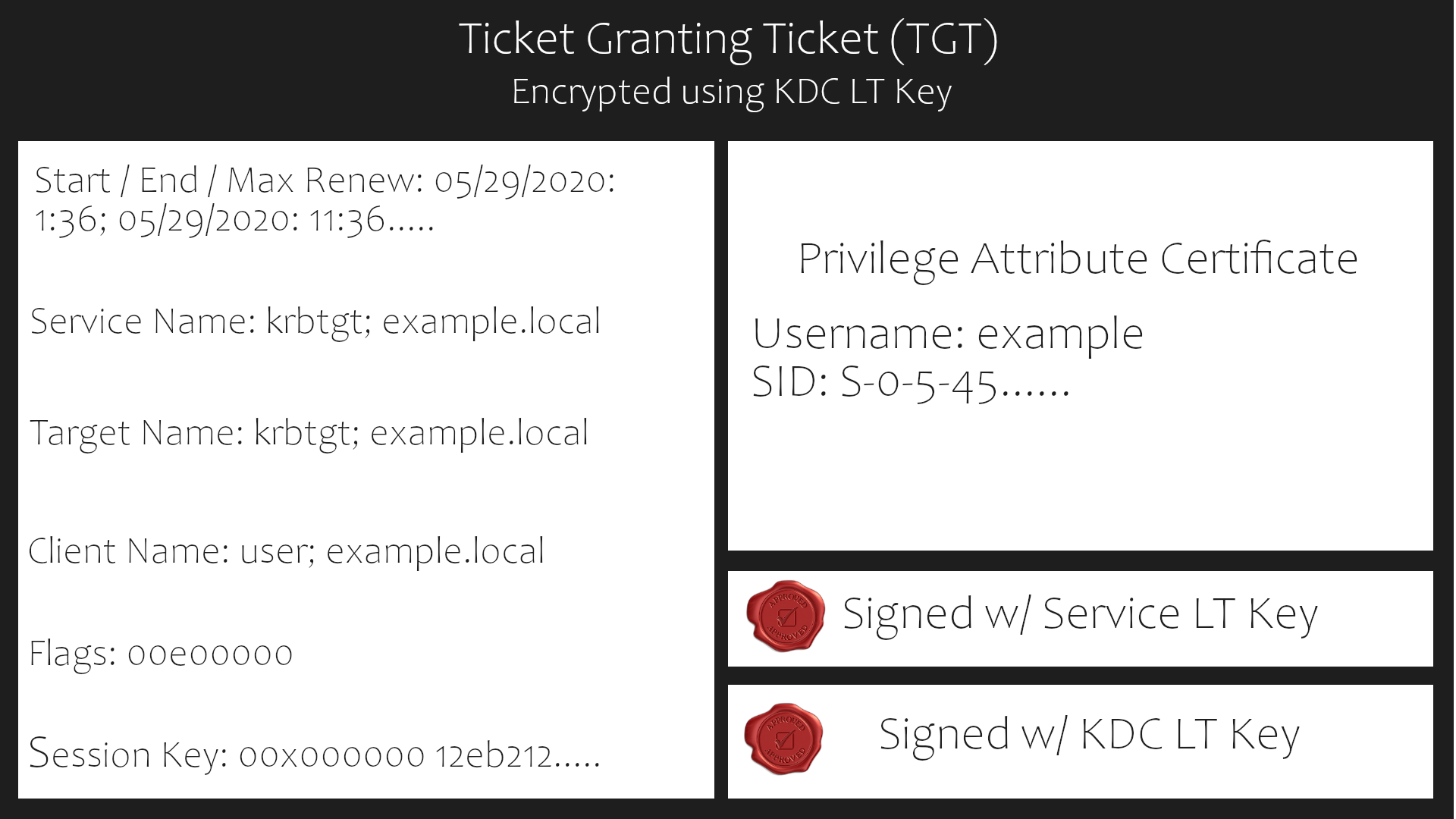
- KDC Long Term Secret Key (KDC LT Key) - The KDC key is based on the KRBTGT service account. It is used to encrypt the and sign the PAC.
- Client Long Term Secret Key (Client LT Key) - The client key is based on the computer or service account. It is used to check the encrypted timestamp and encrypt the session key.
- Service Long Term Secret Key (Service LT Key) - The service key is based on the service account. It is used to encrypt the service portion of the service ticket and sign the PAC.
- Session Key - Issued by the KDC when a is issued. The user will provide the session key to the KDC along with the when requesting a service ticket.
- Privilege Attribute Certificate (PAC) - The PAC holds all of the user's relevant information, it is sent along with the to the KDC to be signed by the Target LT Key and the KDC LT Key in order to validate the user.
AS-REQ w/ Pre-Authentication In Detail -
The AS-REQ step in authentication starts when a user requests a from the KDC. In order to validate the user and create a for the user, the KDC must follow these exact steps. The first step is for the user to encrypt a timestamp NT hash and send it to the AS. The KDC attempts to decrypt the timestamp using the NT hash from the user, if successful the KDC will issue a as well as a session key for the user.
Ticket Granting Ticket Contents -
In order to understand how the service tickets get created and validated, we need to start with where the tickets come from; the is provided by the user to the KDC, in return, the KDC validates the and returns a service ticket.
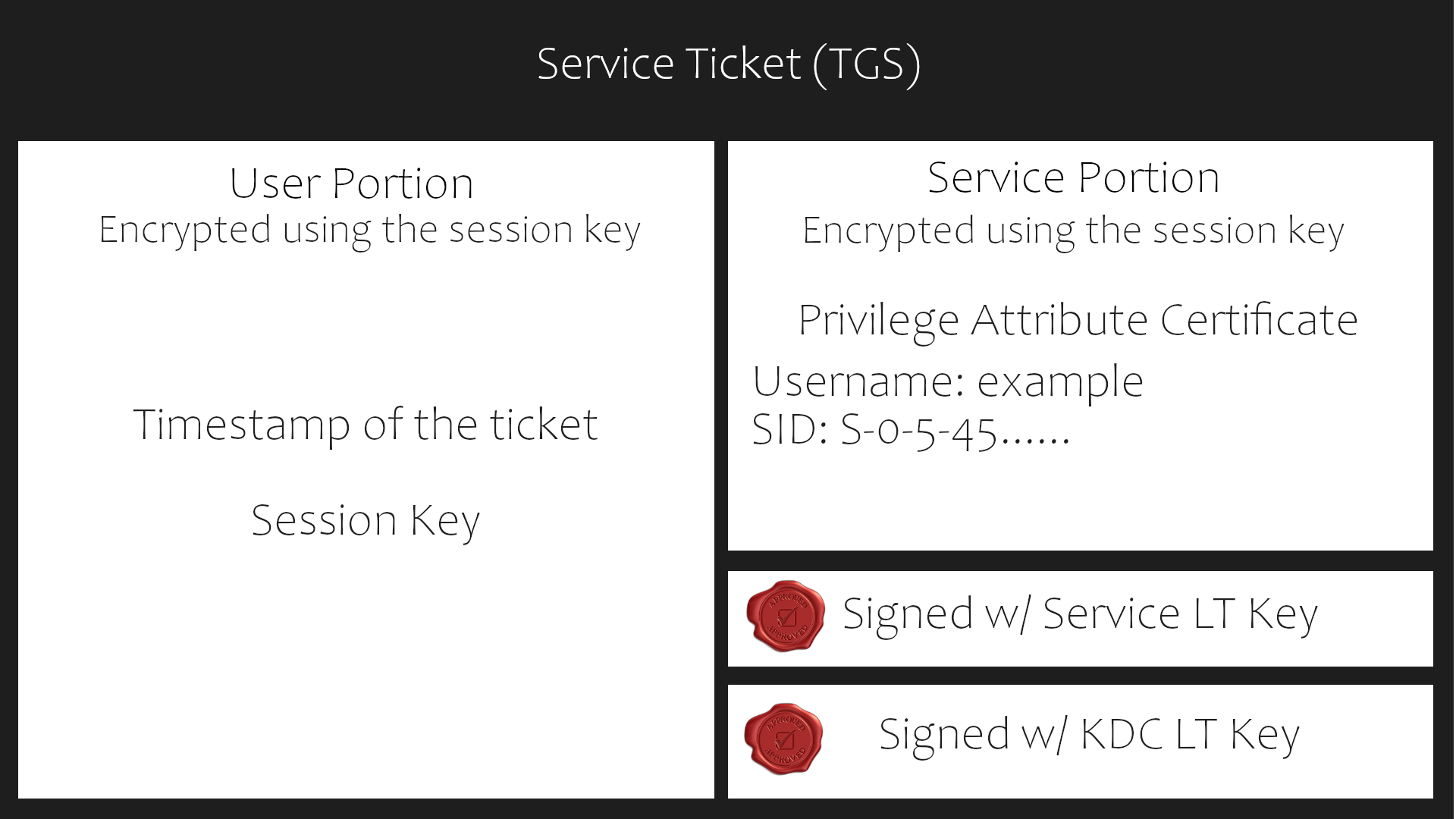
Service Ticket Contents -
To understand how authentication works you first need to understand what these tickets contain and how they're validated. A service ticket contains two portions: the service provided portion and the user-provided portion. I'll break it down into what each portion contains.
- Service Portion: User Details, Session Key, Encrypts the ticket with the service account hash.
- User Portion: Validity Timestamp, Session Key, Encrypts with the session key.
Authentication Overview -
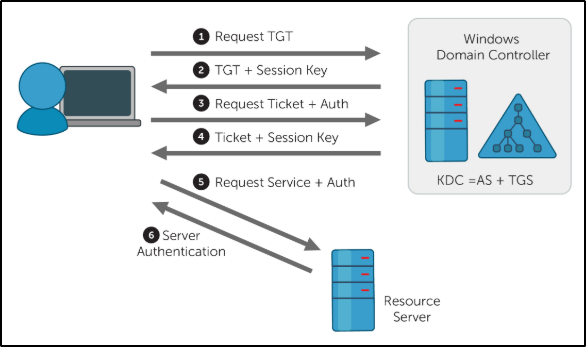
AS-REQ - 1.) The client requests an Authentication Ticket or Ticket Granting Ticket ().
AS-REP - 2.) The Key Distribution Center verifies the client and sends back an encrypted .
TGS-REQ - 3.) The client sends the encrypted to the Ticket Granting Server (TGS) with the Service Principal Name (SPN) of the service the client wants to access.
TGS-REP - 4.) The Key Distribution Center (KDC) verifies the of the user and that the user has access to the service, then sends a valid session key for the service to the client.
AP-REQ - 5.) The client requests the service and sends the valid session key to prove the user has access.
AP-REP - 6.) The service grants access
Tickets Overview -
The main ticket you will receive is a ticket-granting ticket (). These can come in various forms, such as a .kirbi for Rubeus and .ccache for Impacket. A ticket is typically base64 encoded and can be used for multiple attacks.
The ticket-granting ticket is only used to get service tickets from the KDC. When requesting a from the KDC, the user will authenticate with their credentials to the KDC and request a ticket. The server will validate the credentials, create a and encrypt it using the krbtgt key. The encrypted and a session key will be sent to the user.
When the user needs to request a service ticket, they will send the and the session key to the KDC, along with the service principal name (SPN) of the service they wish to access. The KDC will validate the and session key. If they are correct, the KDC will grant the user a service ticket, which can be used to authenticate to the corresponding service.
Attack Privilege Requirements -
- Kerbrute Enumeration - No domain access required
- Pass the Ticket - Access as a user to the domain required
- Kerberoasting - Access as any user required
- AS-REP Roasting - Access as any user required
- Golden Ticket - Full domain compromise (domain admin) required
- Silver Ticket - Service hash required
- Skeleton Key - Full domain compromise (domain admin) required
This Machine can take up to 10 minutes to boot
and up to 5 minutes to or into the machine
What does TGT stand for?
What does SPN stand for?
What does PAC stand for?
What two services make up the KDC?
Deploy the Machine
Ready to learn Cyber Security?
The Attacking Kerberos room is only available for premium users. Signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment.
Already have an account? Log in
