To access material, start machines and answer questions login.
Welcome to the world of securing Operational Technology () and Industrial Control Systems () against cyberattacks!
Most people are familiar with Information Technology (IT) systems, which they interact with daily:
- Laptops and workstations for completing spreadsheets, writing documents, and playing games.
- Servers that store our files and provide services the business needs to operate.
- Websites we visit to do our jobs, learn, buy something, or waste time.
- Smartphones that we can do all of these things from, and so much more!
And yet, many are unaware of the hidden world of Operational Technology () and Industrial Control Systems () that provide the critical services we rely on in our daily lives.
- How does cyber security work in a power plant to prevent an attack from causing a blackout?
- Do power plants even have computers?
- Surely they must, right? But, if they do, how are those computers used to generate electricity?
- And how do we protect critical infrastructure, such as power plants, from cyberattacks?
Learning Objectives
In this first room, you will:
- Learn the differences between IT and /
- Be able to explain the basics of how an environment works
- Understand the main systems that are found in critical infrastructure such as power plants, water treatment facilities, and manufacturing plants
- See the role human operators play in these types of specialized environments
- Comprehend the basics of how cyber security is essential to safe, reliable operations in critical infrastructure
Prerequisites
While there are no formal prerequisites for this room, we do recommend taking the Presecurity path to have a basic understand of various IT concepts that are mentioned in this room.
Let's get started!
Operational Technology ()
Operational Technology () is the use of computers to monitor and control physical equipment and processes in the real world.
Such processes could include:
- A generator inside a power plant that spins to create electricity.
- A conveyor belt that moves parts within a manufacturing plant.
- Computers that operate medical equipment such as MRI and CT scanners.
- Safety systems that prevent a train from overturning when taking a curve too fast.
- Building management systems that control elevators, badged door access, HVAC, and lighting.
- Embedded computers in cars control systems such as engine control, Anti-lock Braking Systems (ABS), and Electronic Stability Control (ESC).

Industrial Control Systems ()
Industrial Control Systems () are a specific type of system found in industrial environments.
Industrial environments include:
- Power plants
- Oil refineries
- Steel mills
- Food packaging facilities
- Pharmaceutical manufacturing
- Water treatment plants
Environments such as hospitals and cars are not considered industrial environments. Systems that are used in these environments to monitor and manage physical equipment and processes are only considered , not , though you’ll find people often use the term interchangeably.
Supervisory Control and Data Acquisition ()
Supervisory Control and Data Acquisition () is a type of used over a wide-area network to monitor and control remote equipment and processes. Examples of wide-area network connections include 5G cellular connections, microwave radio links, and satellite connections.
is used to monitor and control equipment in remote environments that can only be reached with WAN technologies, such as:
- Electric substations
- Offshore oil rigs
- Pipeline pumping stations
- Offshore wind farms
- Remote solar farms
Other terms you might hear that refer to different specific types of include Cyber-Physical Systems (CPS), Industrial Automation and Control Systems (IACS) / Automation and Control Systems (ACS).
In this room, the term is used to represent all of these other terms, including and .
What does the 'O' in OT stand for?
What does the 'C' in ICS stand for?
What Does Do?
monitors and controls physical processes and equipment in the real world.
For example, if I have a power plant, the plant itself uses to monitor and control the process of generating electricity. At a water treatment facility, would be used to monitor and control the process of making water safe to drink and delivering it to customers.
Programmable Logic Controllers (PLCs)
systems, such as Programmable Logic Controllers (PLCs), the most common type of asset deployed today, have both inputs and outputs.
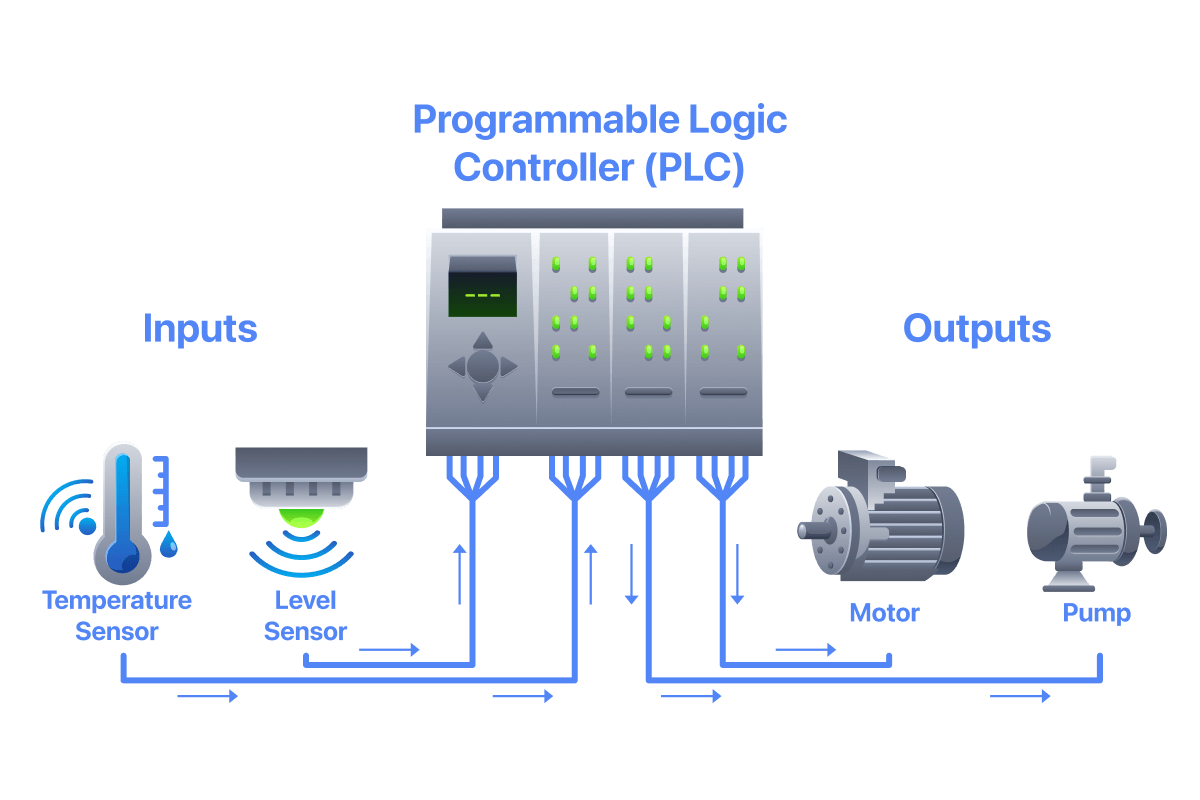
Think of a as a thermostat for an air conditioner you might have at your home or office. This thermostat has a sensor that continually reads the temperature to determine the room temperature. A is programmed with logic so that if the room temperature exceeds the desired temperature, also referred to as the setpoint, it will send a signal to turn on the air conditioning unit.
Inputs
Inputs are pathways that bring data into the from sources such as sensors that monitor conditions in a particular environment. Common types of sensors include, but are not limited to:
- Measure the temperature inside a furnace
- Measure how full an oil storage tank is
- Detect if a dangerous overpressure situation is occurring
- Detect changes in vibration patterns to identify physically failing equipment that needs to be replaced
Outputs
Outputs are pathways that allow the system to send signals to physical systems in the real world, such as pumps, valves, and motors. In our example of an air conditioning unit, once the thermostat determines that the room has reached the desired temperature, it sends a signal via an output to turn off the air conditioning unit.
We will discuss PLCs and other / assets in greater detail in later rooms.
When a PLC needs to send a signal to turn off a motor in the real world, it sends a signal through what type of connection?
What source provides the environmental data that inputs feed into a PLC?
Where Does Cyber Risk Come From in /?
Modern / environments leverage traditional IT technologies, such as Ethernet, /IP, cloud-based services, and GenAI, to improve performance and efficiency in plants and factories. While these technologies bring significant business advantages to the environment, each also introduces vulnerabilities that attackers and other types of cyber security risks could exploit.
IT vs. Infrastructure Comparison
But it's also important to keep in mind how IT and assets, and other infrastructure, are different.
| Feature | IT Infrastructure | Infrastructure |
| Primary Focus | Managing data and information | Managing physical processes and machinery |
| Top Priority | Confidentiality | Safety (human & environmental) |
| Asset Lifespan | Short (3 - 5 years). Hardware is often replaced | Long (10 - 30+ years). Legacy systems are very common |
| Patching | Regular, scheduled updates are standard | Difficult or rare; requires expensive downtime |
| Response to Failure | Rebooting is acceptable | Rebooting can cause safety issues or physical damages |
assets, such as PLCs, are now assigned IP addresses to connect to the network and communicate with other systems. For example, a Human Machine Interface () is a graphical interface used by human operators to monitor a physical process, which is in turn controlled by a . The human operator uses the not only to visually monitor how the process is operating, but also to make adjustments, such as in response to an alert.
What type of damage could an attacker do if they gained access to a plant network and accessed an ?
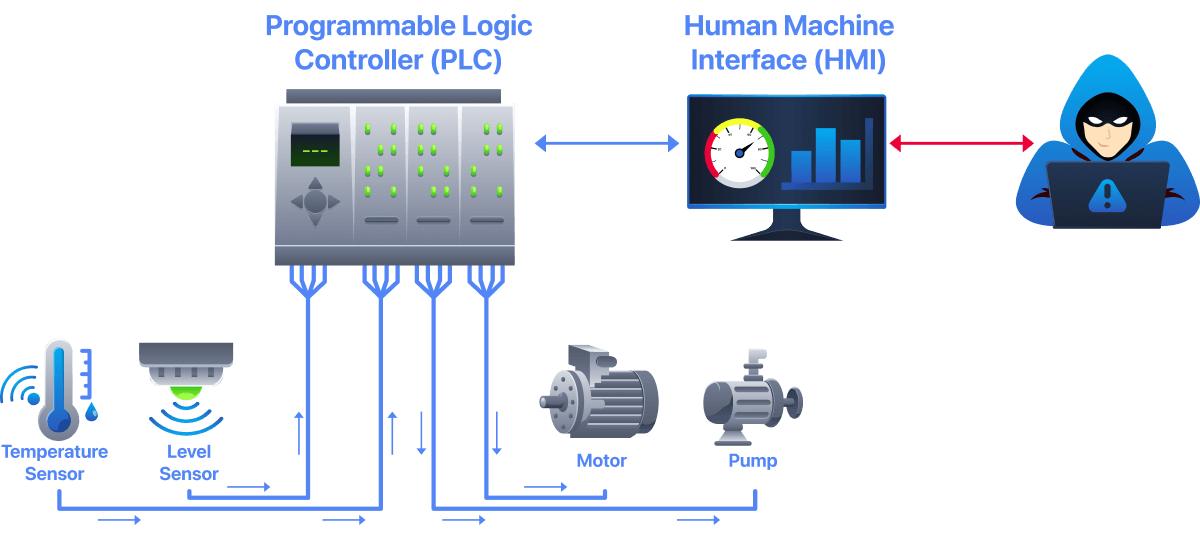
What Could Happen?
Could they:
- Stop power generation to create a blackout?
- Poison water in a water treatment facility?
- Cause systems to physically break down?
- Prevent food from being packaged safely and sent to stores?
All of these types of scenarios can happen, and so many others. In fact, the situations listed above are just a small list of the types of / cyber security incidents that have already happened.
Cyber Security is a Necessity in /
/ cyber security is necessary to ensure the safety and availability of / environments. As the number of cyber-attacks targeting / networks (and the connected IT networks) has nearly doubled each year since the Colonial Pipeline incident (opens in new tab) in 2021, defenders of these specialized environments are woefully underprepared to defend against attackers. But it is possible, and it doesn’t have to be hard!
What type of system is used by a human operator to interact with a PLC and control a physical process in the real world?
Which 2021 incident marked a turning point for OT/ICS security, after which annual cyberattacks against these networks doubled?
IT and Cyber Security Have More in Common Than They Don't!
Many cyber security professionals might tell you that and IT cyber security have nothing in common. But that is the furthest thing from the truth. and IT cyber security actually have much more in common than they don’t.
What is critical is to understand where and IT cyber security are different and how they are different. Because if you are not aware of those differences, you could get someone hurt or killed, let alone take down a plant in the middle of operations.
IT Cyber Security
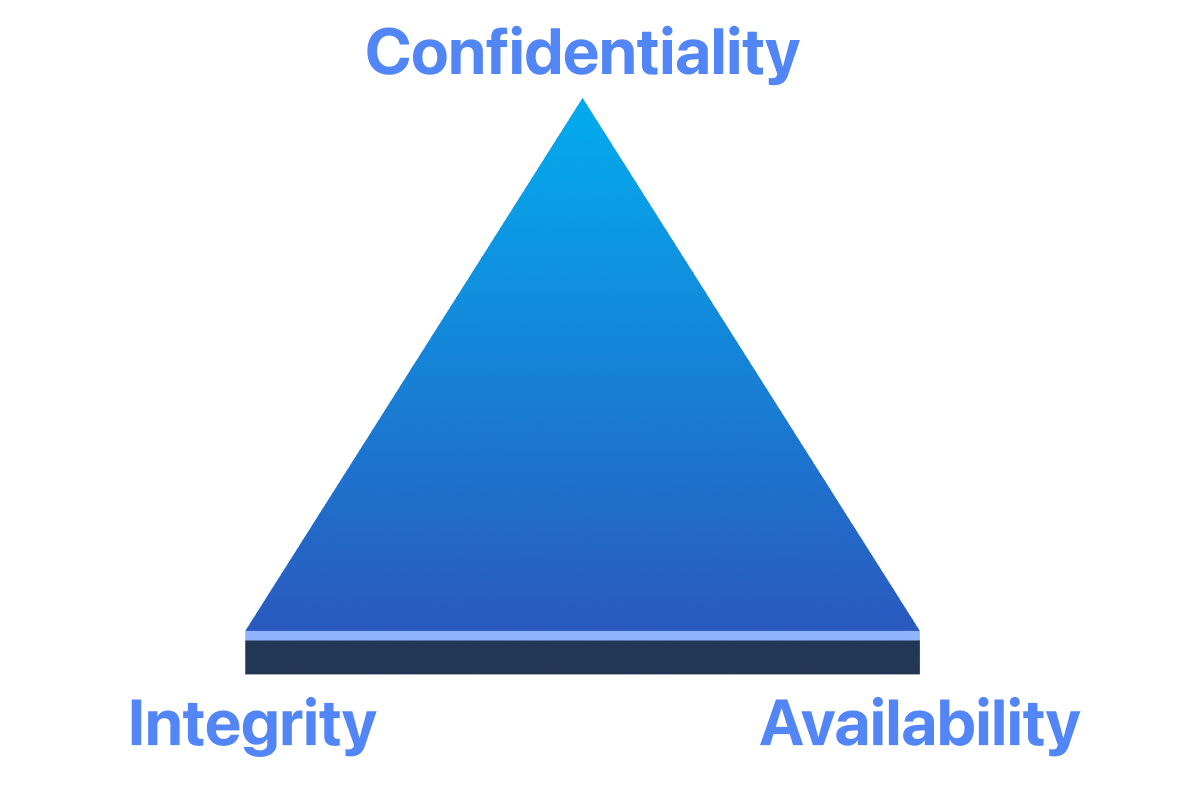
In IT cyber security, the primary requirements are formed by the C-I-A triad.
Cyber Security
In cyber security, many say the requirements are reversed, so we now have an A-I-C triad. Unfortunately, this formula leaves out the most important requirement in cyber security – physical safety. We must ensure that not only do on-site employees go home safe at the end of the day without getting hurt or killed, but that the general public and the environment surrounding the plant are not harmed as well.
Every action we take to defend / networks from cyberattacks focuses first on ensuring physical safety, then on operational availability of the site, the of its data, and, finally, confidentiality. In many / environments focused solely on safety and operational availability, / networks often lack encryption!

How IT and Cyber Security Compare
The following table highlights some of the significant differences between IT and cyber security.
| Security Task | IT Environment (Back Office) | Environment (Factory/Plant) |
| Patch Management | Automatic/Frequent (patches are rolled out almost as soon as they are released) | Planned/Rare (patching requires halting production which occurs rarely (e.g., once a year) in scheduled maintenance windows.) |
| Vulnerability Scanning | Active Scanning (networks can be probed for existing vulnerabilities) | Passive Monitoring (active scanning with tools like and Nessus can cause assets to crash) |
| Incident Response | Isolate & Reboot (If a system is compromised, we wipe it and reinstall) | Keep it Running ( systems cannot simply be isolated or rebooted without introducing safety and operational availability issues) |
| Network Encryption | Almost Everything (Almost all network traffic in IT networks is encrypted to ensure confidentiality) | Very Low (Most / protocols do not support encryption; while newer protocols do, most plants continue to favor older unencrypted ones) |
What is the most important requirement for OT/ICS cyber security?
What do many OT environments not leverage?
Bringing It All Together
In this task, you will access the Human Machine Interface () for a specific type of / environment. You will use the interface and information presented to think and respond as a human operator would in this environment. Open the static site by clicking the View Site button in the upper right corner and then proceed to solve the questions below.
Based on a review of the HMI, what type of environment is this?
When you first look at the HMI, what is the current percentage level indicated by the tank level sensor?
Click on the START button to turn on the pump to bring more water into the tank. At what percentage level do you first receive an alert in a yellow warning banner?
Continue to allow water to flow into the tank. At what percentage level does the control system realize there is danger and shuts off the pump bringing water into the tank?
With the pump stopped, click OPEN on the valve on the outtake pipe. What happens to the water level in the tank? The water level <fill in the blank>.
Nice job getting started on learning how to protect and environments from cyberattacks!
In this room, you learned about the differences between IT and , how and systems are part of , how cyber security can be similar but different from IT, and the important role human operators play in environments.
This room was created by the incredible Mike Holcomb. You can find more information on his work here. (opens in new tab)
Nice job completing the room!
Ready to learn Cyber Security?
TryHackMe provides free online cyber security training to secure jobs & upskill through a fun, interactive learning environment.
Already have an account? Log in