To access material, start machines and answer questions login.
Introduction
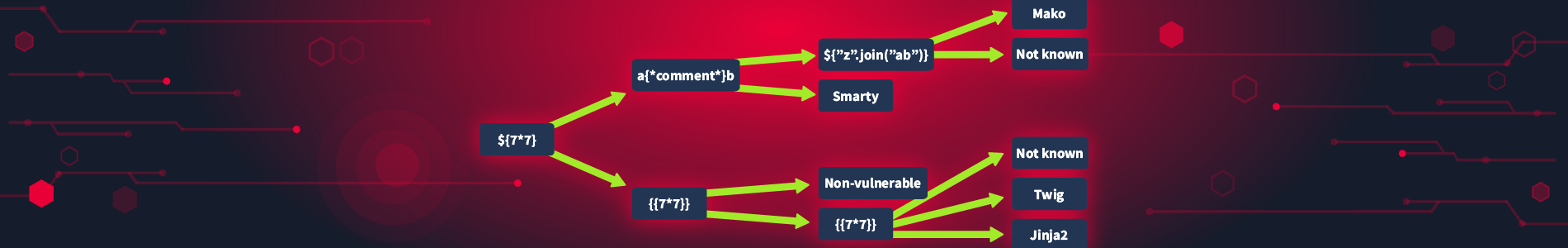
Server-side template Injection, or SSTI, is a vulnerability that occurs when user input is injected into a template engine of an application. This can lead to a range of security issues, including code execution, data exposure, privilege escalation, and Denial of Service (). SSTI vulnerabilities are often found in web applications that use template engines to generate dynamic content and can have serious consequences if left unaddressed.
An introductory room about SSTI can be found here.
Objectives
By the end of this room, you will:
- Understand the basic functions of template engines and why they are integral to modern web applications.
- Identify vulnerabilities within web applications that can lead to SSTI.
- Execute attacks on different template engines such as Smarty (), Jinja2 (Python), and Jade (NodeJS).
- Apply best practices and mitigation strategies to prevent SSTI in web applications.
Prerequisites
Before diving into SSTI, you should have a basic understanding of the following concepts:
- Knowledge of HTML structure and how web pages are built.
- Basic understanding of JavaScript for client-side scripting.
- Familiarity with server-side programming concepts and languages (e.g., Python, , JavaScript).
Note: This room contains a non-guided challenge in Task 8. You must use the knowledge learned in this room and basic offensive security skills to complete the challenge!
Add MACHINE_IP to your /etc/hosts file. For example:
MACHINE_IP ssti.thm
After 3 minutes, visit http://ssti.thm to access the machine.
Ready to learn Cyber Security?
The Server-side Template Injection room is only available for premium users. Signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment.
Already have an account? Log in