0%
Linux Logging for SOC
Explore key Linux log sources and learn how to use them in your SOC triage.
0%
Linux Threat Detection 1
Explore how attackers break into Linux systems and how you can detect this in logs.
0%
Linux Threat Detection 2
Explore the first actions of attackers after breaching a Linux server and learn how to detect them.
0%
Linux Threat Detection 3
Cover the last stages of attacks on Linux and learn how they look in system logs.
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
0%
BlackCat
BlackCat claims to have breached your company and posted proof on their leak site. As the SOC analys...
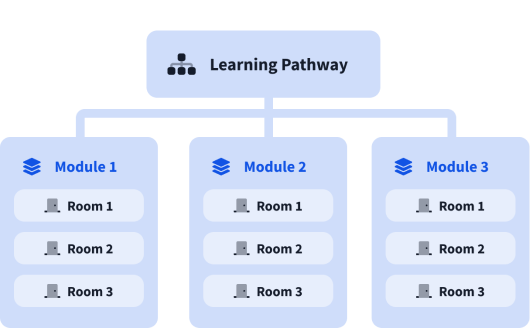
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).