0%
Red Team Recon
Learn how to use DNS, advanced searching, Recon-ng, and Maltego to collect information about your target.
0%
Weaponization
Understand and explore common red teaming weaponization techniques. You will learn to build custom payloads using common methods seen in the industry to get initial access.
0%
Password Attacks
This room introduces the fundamental techniques to perform a successful password attack against various services and scenarios.
0%
Phishing
Learn what phishing is and why it's important to a red team engagement. You will set up phishing infrastructure, write a convincing phishing email and try to trick your target into opening your email in a real-world simulation.
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
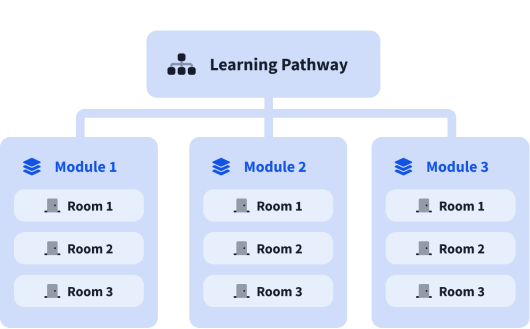
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).