0%
Chaining Vulnerabilities
Learn how to chain vulnerabilities! From Low to High!
0%
Extract
Can you extract the secrets from the library?
0%
Voyage
Chain multiple vulnerabilities to gain control of a system.
0%
Sequence
Chain multiple vulnerabilities to take control of a system.
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
Need to know

Advanced Server-Side Attacks
Master the skills of advanced server-side attacks, covering SSRF, File Inclusions, Deserialization, Race Conditions, and Prototype Pollution.

Advanced Client-Side Attacks
Through real-world scenarios, you will gain a detailed understanding of client-side attacks, including XSS, CSRF, DOM-based vectors, SOP, and CORS vulnerabilities.

Web Hacking Fundamentals
Understand the core security issues with web applications, and learn how to exploit them using industry tools and techniques.
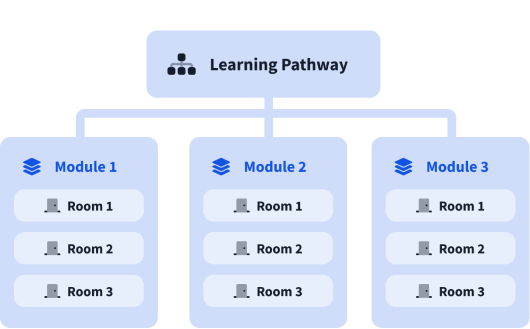
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).