0%
Active Directory Basics
This room will introduce the basic concepts and functionality provided by Active Directory.
0%
Breaching Active Directory
This network covers techniques and tools that can be used to acquire that first set of AD credentials that can then be used to enumerate AD.
0%
Enumerating Active Directory
This room covers various Active Directory enumeration techniques, their use cases as well as drawbacks.
0%
Lateral Movement and Pivoting
Learn about common techniques used to move laterally across a Windows network.
0%
Exploiting Active Directory
Learn common AD exploitation techniques that can allow you to reach your goal in an AD environment.
0%
Persisting Active Directory
Learn about common Active Directory persistence techniques that can be used post-compromise to ensure the blue team will not be able to kick you out during a red team exercise.
0%
Credentials Harvesting
Apply current authentication models employed in modern environments to a red team approach.
Topic Rewind Recap
Lock in what you learned with a recap. Earn points and keep your streak.
Need to know
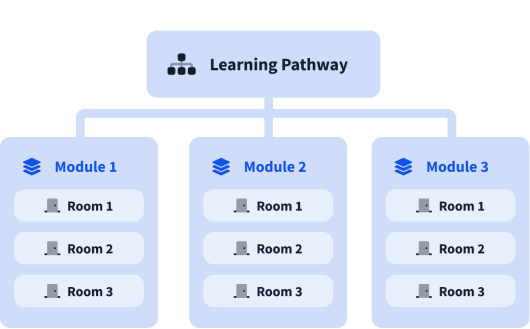
What are modules?
A learning pathway is made up of modules, and a module is made of bite-sized rooms (think of a room like a mini security lab).